The great Exchange Server hacking spree
Four months ago, it was SolarWinds. Now it's Exchange Server.
It feels like the dust has barely settled around the sprawling SolarWinds hack, and yet here we are in the midst of yet another one.
Earlier this week, Microsoft rolled out emergency patches to address four previously undisclosed security flaws in Exchange Server email software, which it said were exploited by a group known as Hafnium — a state-sponsored collective operating out of China.
While the Windows maker characterized the attacks as “limited and targeted,” it’s now clear the out-of-band fixes have not deterred the threat group from stepping up its attacks to breach as many organizations as possible before they are patched.
According to independent cybersecurity journalist Brian Krebs and WIRED’s Andy Greenberg, at least 30,000 entities across the U.S. — including small businesses, towns, cities and local governments — have borne the brunt of an “unusually aggressive” Chinese group that has set its sights on stealing emails from victim organizations by exploiting the flaws in Exchange Server.
Following each incident, the cyber spies are said to have left behind a web shell — a web-based backdoor — to remotely control the compromised server. The ultimate goal is to make use of this remote access to conduct reconnaissance on the target machines, and subsequently plunder mailboxes from an organization’s network and export the collected data to file sharing sites like MEGA.
While this implies that the Chinese hackers are likely to escalate their attacks only in select cases, organizations that have been already breached to deploy the web shell continue to remain at risk of future compromise until the malware is completely rooted out.
Here’s the troubling part: “the longer it takes for victims to remove the backdoors, the more likely it is that the intruders will follow up by installing additional backdoors, and perhaps broadening the attack to include other portions of the victim’s network infrastructure.”
FireEye’s Mandiant threat intelligence team said it “observed multiple instances of abuse of Microsoft Exchange Server within at least one client environment” since the start of the year. Cybersecurity firm Volexity, which discovered the flaws and reported to Microsoft, said the intrusion campaigns appeared to have started around January 6, 2021.
Meanwhile, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an emergency directive warning of “active exploitation” of the vulnerabilities, ordering government agencies running vulnerable versions of the software to either update the software or disconnect the products from their networks.
“A massive, massive number of organizations are getting that initial foothold,” Volexity founder Steve Adair told Greenberg. “It’s a ticking time bomb that can be used against them at any point in time.”
The fact that a mass intrusion campaign of this scale is unfolding within four months of the SolarWinds supply chain attack coming to light paints a disturbing trend.
But if there’s any consolation, it’s that the Hafnium Exchange hacks have been detected early unlike the SolarWinds breach, where the adversaries had over a year to silently compromise organizations via trojanized software updates.
“Bad guys exploit [vulnerabilities] all the time,” former CISA director Chris Krebs tweeted. “2020, inter alia, was the year of the bad VPN exploit. But the sheer scale and speed of this one is terrifying. It’s trivial to exploit. Countdown to Ransomware? Remember that whole ‘those that can least afford it thing?’ What happens next?”
What’s trending in Security?
🇲🇲 Following the coup last month, Myanmar’s ruling military is said to have drafted a new cybersecurity legislation that gives the government sweeping powers to access user data without a warrant.
Furthermore, an investigation by The New York Times has revealed a sophisticated arsenal of surveillance drones, phone cracking software developed by Cellebrite, and other hacking tools that are being deployed to crack down on attempts to restore democracy in the country. [ZDNet / The New York Times]
🇷🇺 An elite underground online criminal forum called Maza got compromised by unknown attackers, making it the fourth Russian-language forum to have been breached since the start of the year after Verified, Crdclub, and Exploit. [The Hacker News]
⚠️ Researchers from FireEye and Microsoft found three more malware strains in connection with the SolarWinds attacks. “In all stages of the attack, the actor demonstrated a deep knowledge of software tools, deployments, security software and systems common in networks, and techniques frequently used by incident response teams,” Microsoft said.
In a related development, SolarWinds blamed an intern for a critical password lapse that went unnoticed for several years. The password “solarwinds123” was originally believed to have been publicly accessible via a GitHub repository since June 17, 2018, before the misconfiguration was addressed on November 22, 2019. But company executives testified last week the password had been in use as early as 2017.
All said and done, fully recovering from the SolarWinds hack could take the U.S. government as long as 18 months, Brandon Wales, the acting director of the CISA, said. [The Hacker News / MIT Technology Review]
🔐 Google unequivocally stated it would not build alternate identifiers or intrusive tools to track users across multiple websites once it begins phasing out third-party cookies from its Chrome browser by early 2022. Instead, the search giant intends to use a machine learning methodology called Federated Learning of Cohorts (FLoC) to serve targeted ads. The Electronic Frontier Foundation called it “a terrible idea” that creates new privacy risks. [The Hacker News]
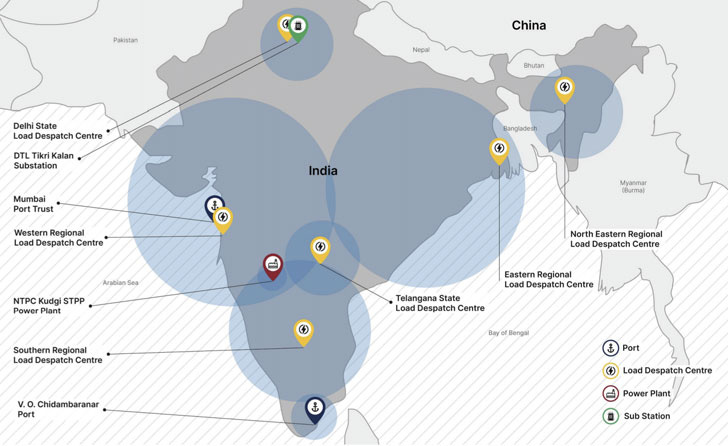
🇮🇳 Chinese state-sponsored groups were found targeting India’s power grid amid heightened border tensions between India and China last year. “10 distinct Indian power sector organizations, including four of the five Regional Load Despatch Centres (RLDC) responsible for operation of the power grid through balancing electricity supply and demand, have been identified as targets in a concerted campaign against India’s critical infrastructure,” Recorded Future said in a report. [The Hacker News]
🐛 A new sample of Ryuk ransomware spotted in January 2021 appears to have gained worm-like capabilities, allowing it to propagate from machine to machine without any human interaction within an internal network. [ANSSI]
🇨🇳 OneZero goes into detail about “Sharp Eyes,” a computerized video surveillance program that aims to keep tabs on 100% of Chinese public spaces and relies largely on reports from citizens. [OneZero]
🔎 The GootKit malware has undergone what researchers call a “renaissance” when it comes to payload delivery to become an increasingly sophisticated loader framework. It’s now using a known tactic for malware delivery called search engine optimization (SEO) poisoning to rank compromised sites higher in Google search results, which contain links that launch the Gootloader attack chain to deliver a plethora of malicious payloads. [The Hacker News]
📱 Researchers are pointing out that Apple’s walled garden approach to iOS makes it virtually impossible to spot the presence of malware on iPhones, giving resourceful attackers a way to take advantage of Apple’s “impenetrable” defenses and evade detection. [MIT Technology Review]
👀 Invisible pixels used to track email activity are now an “endemic” issue that breaches users’ privacy. Email pixels can, among other things, let senders know if and when an email is opened, how many times it’s opened, what devices are used, and the recipient’s rough physical location. [BBC]
🌐 One more reason why you should be cautious about installing browser extensions. Journalist ran Krebs unmasks a shady Singapore-based firm called Infatica that offers to buy popular brow extensions or pay the developers to silently include some extra code that could allow it to inject “whatever they wanted.” [Krebs on Security]
🚨 AdGuard published a list of over 6,000 trackers abusing the CNAME cloaking technique, which lets trackers bypass many ad-blocking and anti-tracking protections. [AdGuard]
☁️ According to a new analysis by Zimperium, 14% of Android and iOS apps connecting to cloud services like AWS or Azure, totaling about 19,000 apps, have misconfigurations that expose user data. [WIRED]
🗃 The past fortnight in data breaches, leaks, and ransomware: Bharat Biotech, CompuCom, Gab, Lactalis, Malaysia Airlines, Oxfam Australia, Qualys, Serum Institute of India, Ticketcounter, and COVID-19 lab test results from the Indian state of West Bengal.
2,000%
That’s the increase in malware written in Go language since 2017. According to a new report published by Intezer, this change is attributed to the fact that Go-based malicious binaries are hard to analyze and reverse engineer, not to mention support for “a very well-written networking stack that is easy to to work with.”
That’s it for now. See you all in a week. Stay safe!
-Ravie