CIA's "bulk" collection program revealed
A newly declassified report reveals there was no oversight
Two U.S. Democratic senators, Ron Wyden of Oregon and Martin Heinrich of New Mexico, released a declassified report called Deep Dive II that shows the Central Intelligence Agency (CIA) has for years been collecting some Americans’ data in bulk, without a warrant or any congressional approval or oversight as part of a mass surveillance dragnet.
The specifics about the data were not disclosed, how much information was amassed, or what technology was used to facilitate the collection. It also does not say when the clandestine program took place, and whether those activities are still ongoing.
“It has done so entirely outside the statutory framework that Congress and the public believe govern this collection, and without any of the judicial, congressional or even executive branch oversight that comes with FISA collection,” the letter, which was written in April 2021, read.
What’s trending in security?
👨 The U.S. Internal Revenue Service (IRS) announced it will transition away from the use of third-party facial recognition services that requires taxpayers to upload video selfies when creating new IRS online accounts for the verification of their identities, effectively ending a contract with facial recognition company ID.me that had received widespread criticism. [Ars Technica / CyberScoop]
🚫 Starting in April, Microsoft said it’s planning to block macros obtained from the internet by default for several Office applications, such as Access, Excel, PowerPoint, Visio and Word, on devices running Windows to thwart cybercriminals that try to abuse macros as part of their spear-phishing attacks using specially-themed documents. That said, attackers are expected to "step up their game" in response to Microsoft's security measures around macros. [The Hacker News]
📱 A new report published by Reuters revealed that a now-patched flaw in Apple's software, dubbed FORCEDENTRY, and exploited by Israeli surveillance firm NSO Group to break into iPhones in 2021 was simultaneously abused by a lower profile competing Israeli company called QuaDream.
Both versions of ForcedEntry are so similar that when Apple fixed the underlying flaws in September 2021, it rendered both NSO and QuaDream’s surveillance tools ineffective. Like NSO’s Pegasus spyware, QuaDream’s flagship product called REIGN is capable of taking control over smartphones, activating cameras and microphones, and recording live phone calls.
In a related development, the Israeli government said it would investigate reports that police had illegally used NSO Group’s Pegasus spyware against its own citizens, including phones of Israeli activists, local politicians, businessmen, civil servants, and politicians, without a court order, amid intensifying scrutiny of the spyware company. [The Hacker News / The New York Times]
💵 Jay Freeman, a white-hat hacker and the developer of Cydia and Orchid, was awarded a $2 million bug bounty for finding a critical flaw in the Ethereum Layer 2 scaling project Optimism that could have enabled hackers to create as much Ethereum in an Optimism account balance as they wished. [Jay Freeman / Optimism]
🛡️ Google Cloud launched Virtual Machine Threat Detection in public preview, an opt-in feature that scans VMs for threats including cryptomining malware without requiring customers to install new software on their instances. [Google]
💲 The U.S. Federal Bureau of Investigation said that Americans lost more than $68 million to SIM swapping attacks in 2021. SIM swapping is a malicious technique where criminal actors target mobile carriers to gain access to victims' bank accounts, virtual currency accounts, and other sensitive information. [FBI]
🔐 Google, which took the first step to get its 2-Step Verification (2SV) auto-enrollment plan off the ground last year, said it successfully auto-enabled the feature for over 150 million users and more than two million YouTube creators, resulting in a "50% decrease in accounts being compromised among those users." [Google]
🐲 The Chinese threat actor tracked as Kimsuky has been found leveraging its custom backdoor, Gold Dragon, to drop an open-source remote access and administration tool called xRAT on compromised systems. [ASEC]
🚨 Gamaredon, a known Russia-linked threat group, has been targeting an array of organizations in Ukraine, including government, military, law enforcement, non-profit and judiciary entities, in an attempt to steal sensitive data. [The Hacker News]
🔎 Malicious actors are using search engine optimization (SEO) poisoning, which involves creating phony websites that leverage SEO-friendly keywords and techniques to make them rank higher in search results, as an initial attack vector with the end goal of infecting targets with malware, stealing credentials and more. [The Hacker News]
📩 Hackers are relying on a 20-year-old trick, called Right-to-Left Override (RLO) attack, to trick users into executing a file with a disguised extension as part of a new phishing campaign. By injecting the override, a non-printing Unicode character [U+202e] mainly used to support Hebrew and Arabic languages, a malicious payload like "abc[U+202e]txt.exe" will appear "abcexe.txt" in Windows. [Vade]
🔑 The master decryption keys for the Maze, Egregor, and Sekhmet ransomware operations have been released by the alleged malware developer. [Bleeping Computer]
⚙️ Threat actors are now distributing fake Windows 11 upgrade installers to users of Windows 10, tricking them into downloading and executing RedLine stealer malware, once again demonstrating how attackers rely on topical lures to socially engineer victims into infecting systems. [HP Threat Research]
💶 Cryptocurrency payments to military and hacktivist groups in Ukraine aimed at countering Russian aggression against the country spiked sharply in the second half of 2021, hitting $550,000 last year, compared with just $6,000 or so in 2020, according to blockchain analysis firm Elliptic. [Elliptic]
2⃣️ It’s been a little over two months since Log4Shell, a security flaw in a widely used piece of logging software known as Log4j, came to light. But new findings show that flawed versions of the free tool, accounting for more than a one-third, continue to be downloaded at least tens of thousands of times each day from the Maven software repository. The Log4j vulnerability set off a race for companies to patch their computer systems and highlighted the need for securing the open-source supply chain. [The Wall Street Journal]
🌐 Researchers have devised a new framework called WebSpec for the “analysis of browser security mechanisms, which enables both the automatic discovery of logical flaws and the development of machine-checked security proofs.” [arXiv]
💳 A special law enforcement operation undertaken by the Russian government has led to the seizure and shutdown of four online bazaars — Ferum Shop, Sky-Fraud, Trump's Dumps, and UAS — that specialized in the theft and sales of stolen credit cards. The development is the latest in a series of closures on the dark web, a part of the internet that can only be accessed with special software and that is known for hosting illegal activity. Previously, UniCC’s sudden closure last month was speculated as motivated by a desire to avoid increased law enforcement scrutiny after the shuttering of similar illicit online marketplaces in the preceding months. [The Hacker News]
🗄️ The past week in data breaches, leaks, and ransomware: Light Collective, Pop TV, Puma, Vodafone Portugal, the U.K. government’s Foreign Office, and the U.S. State of Washington.
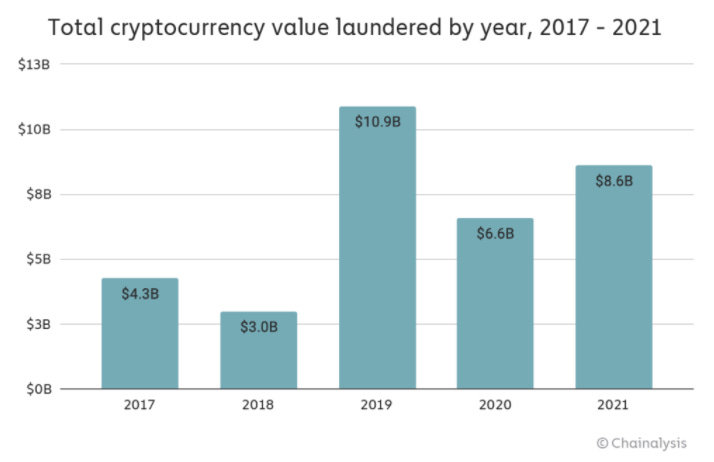
$8.6 billion
That’s the total amount of money cybercriminals laundered in cryptocurrencies in 2021, up 30% from 2020, according to a new report from blockchain analytics firm Chainalysis. The ill-gotten currencies were derived from crypto-native crimes such as darknet market sales or ransomware attacks in which profits are in crypto instead of fiat currencies.
Tips, Comments, Ideas?
Send them my way by writing replying to this email.
Thanks again for reading. See you in the next edition!