Yet another darknet market bites the dust
Law enforcement ramps up efforts to tackle illicit online activity
U.S. law enforcement earlier this month announced the takedown of SSNDOB, a notorious market used for trading the personal information — including Social Security numbers, or SSNs — of nearly 24 million Americans, marking another in a chain of dark web seizures in the past year. The marketplace has received nearly $22 million worth of Bitcoin across over 100,000 transactions since April 2015.
The figures also suggest that some users were buying personally identifiable information from the service in bulk, according to Chainalysis, which also uncovered a connection between SSNDOB and Joker’s Stash. The operators of SSDOB are said to have employed various techniques to protect their anonymity and to thwart detection of their activities.

Services like SSNDOB can have severe consequences in that cybercriminals who purchase this information could then use it for a number of malicious purposes, including to conduct phishing attacks and scam campaigns and to create fraudulent online identities.
Chainalysis also noted that the SSNDOB shutdown is “the latest in a string of darknet market closures over the past year [and] illicit services that embrace cryptocurrency have opened themselves up to law enforcement scrutiny and been shut down, in large part because of the inherent transparency of blockchains.”
That’s not all. The U.S. Justice Department revealed that RSOCKS, a popular web proxy service that allowed buyers to route their traffic through a range of different IP addresses, was actually a front by Russian cybercriminals, and the 8 million claimed IP addresses that the service used as proxy servers were hacked devices that had been ensnared as part of a giant botnet to hide malicious traffic and activity.
What’s trending in security?
🐘 Earlier this February, SentinelOne disclosed that a previously unknown hacking group known as ModifiedElephant had been linked to targeted attacks against human rights activists, human rights defenders, academics, and lawyers across India in an attempt to plant “incriminating digital evidence,” leading to their arrests in January 2021. This has now been confirmed to be the work of a police agency in Pune in an attempt to frame and jail the human rights activists. [WIRED]
🎶 An interesting story worth a read about how U.S. saxophonist Merryl Goldberg came up with a custom encryption scheme that used musical notation to allow her to smuggle information into and out of the former USSR. “To create the code, Goldberg assigned letters of the alphabet to notes in the chromatic scale, a 12-tone scale that includes semi-tones (sharps and flats) to expand the possibilities,” the story goes. [WIRED]
💣 Joshua Schulte was once employed making cyberweapons for the U.S. Central Intelligence Agency (CIA). Feeling wronged by the agency after a dispute with a colleague, he allegedly retaliated by releasing troves of secret data on WikiLeaks, exposing U.S. hacking methods and assets, representing the single largest leak of classified information in the agency’s history. [The New Yorker]
🛑 A never-before-seen Linux backdoor has been spotted using novel evasion techniques to camouflage its presence on infected hosts. Dubbed Symbiote, domain names used by the malware indicates the threat actors are currently impersonating Brazilian banks, which suggests that these banks or their customers are potential targets. It was first detected in November 2021. The eminently capable piece of malware, which “parasitically” infects all running processes, operates as a rootkit, a remote access backdoor, and can execute commands with the highest privileges and can harvest credentials. It is also a shared object library, instead of an standalone executable file.
What’s more, another newly discovered stealthy piece of Linux malware called Syslogk has been observed delivering a backdoor that remains dormant on the targeted machine until its controller, from anywhere on the internet, awakens it by transmitting so-called “magic packets.” [The Hacker News]
🛡️ Microsoft said it obtained a court order to seize 41 domains used by what the Windows giant said was an Iranian cybercrime group that ran a spear-phishing operation targeting organizations in the US, Middle East, and India. [The Hacker News]
U.S. cybersecurity and intelligence agencies warned that publicly known flaws within network devices such as routers, NAS appliances, VPNs are being be exploited by Chinese government-backed threat actors as part of broader attacks to break into a wide range of public and private sector targets. [The Hacker News / MIT Technology Review]
🤖 Researchers have uncovered a new Android malware threat codenamed “MaliBot” that’s capable of exfiltrating financial and personal information after taking control of infected devices. The trojan also gathers the list of applications installed, which is used to identify overlays/injections that can be used on top of applications that the user is launching to siphon credentials. [The Hacker News]
💲 Microsoft is warning that BlackCat ransomware infections embrace different tactics to deliver the payload depending on the affiliate group conducting the attack, throwing a wrench in the ability to adequately detect such intrusions. [The Hacker News]
🚨 Researchers have disclosed a novel hardware attack dubbed “PACMAN” targeting Apple’s M1 chips that can bypass a security mechanism called pointer authentication and achieve remote code execution. The method, at its core, combines memory corruption and speculative execution to carry out a control-flow hijacking attack. That said, there is no immediate cause for concern as no end-to-end attacks have been devised and requires an existing memory corruption flaw.
In a related development, a new “Hertzbleed” chip vulnerability has been found to allow side channel attacks that can steal secret AES cryptographic keys. Hertzbleed works by observing or exploiting a secondary effect of an operation on a system, in this case the power signature of any given cryptographic workload. An attacker can convert that power fluctuation information to timing data, allowing them to steal cryptographic keys. Cryptographic implementations that are already hardened against power side channel attacks aren’t susceptible to the Hertzbleed vulnerability. [The Hacker News]
💥 Sanctions the U.S. government imposed on Russia-based crimeware gang Evil Corp in 2019 have forced the threat actor to evolve its tactics to remain in the cybercrime business. After previously observed deploying ransomware families such as Hades, WastedLocker, and Phoenix, the group has now pivoted to using off-the-shelf ransomware like LockBit. The intrusions have been attributed to a cluster sharing numerous overlaps with Evil Corp.
The shift to a ransomware-as-a-service model, the researchers say, is both an attempt to obscure attribution and sidestep sanctions. If anything, the RaaS model is yet another indicator as to how it enables cybercriminal gangs to anonymously carry out their operations. The U.S. Treasury sanctioned Evil Corp in 2019 for its development and distribution of Dridex. [The Hacker News]
⚠️ A key hallmark of any successful advanced persistent threat (APT) group is its ability to operate undetected for years by evolving and adapting its TTPs over time. The newest example is “Aoqin Dragon,” a China-based threat actor that has been linked to espionage attacks in Australia and Southeast Asia for the past 10 years. [The Hacker News]
👾 Potent malware botnet Emotet has resurfaced with more advanced features after having its infrastructure tore down by law enforcement in January 2021. This includes utilizing 64-bit shell code, as well as more advanced PowerShell, active scripts, and a new module to steal credit card information from Chrome browsers. [The Hacker News / Deep Instinct]
🔍 A newly discovered mobile spyware — used by governments — has been used to selectively target Android (and iOS) users in Kazakhstan, Italy, and Syria. Dubbed Hermit, it’s modular and impersonates well-known brands, like Oppo and Samsung, with the goal of stealing sensitive information. It’s been attributed to an Italian company named RCS Lab that dabbles in the same market as NSO Group and FinFisher. [The Hacker News]
📵 An Android malware named SMSFactory targeted more than 165,000 users between May 2021 to May 2022, most of them located in Russia, Brazil, Argentina, Turkey, and Ukraine with the goal of subscribing victims to premium services. The apps tend to be distributed via unofficial app stores. [Avast]
🗄️ The past few weeks in data breaches, leaks, and ransomware: AGCO, Americanas, Bulgarian State Agency for Refugees, Carinthia, Chicago Public Schools, CTARS, General Motors, Ikea Canada, Kaiser Permanente, Maiar, Massy Stores, Mobike, Nikkei, Novartis, Parker, Shoprite Group, Sixt, SpiceJet, Texas Department of Insurance, Transport for NSW, Verizon, Yik Yak, Zola, and Greenland’s healthcare systems.
46%
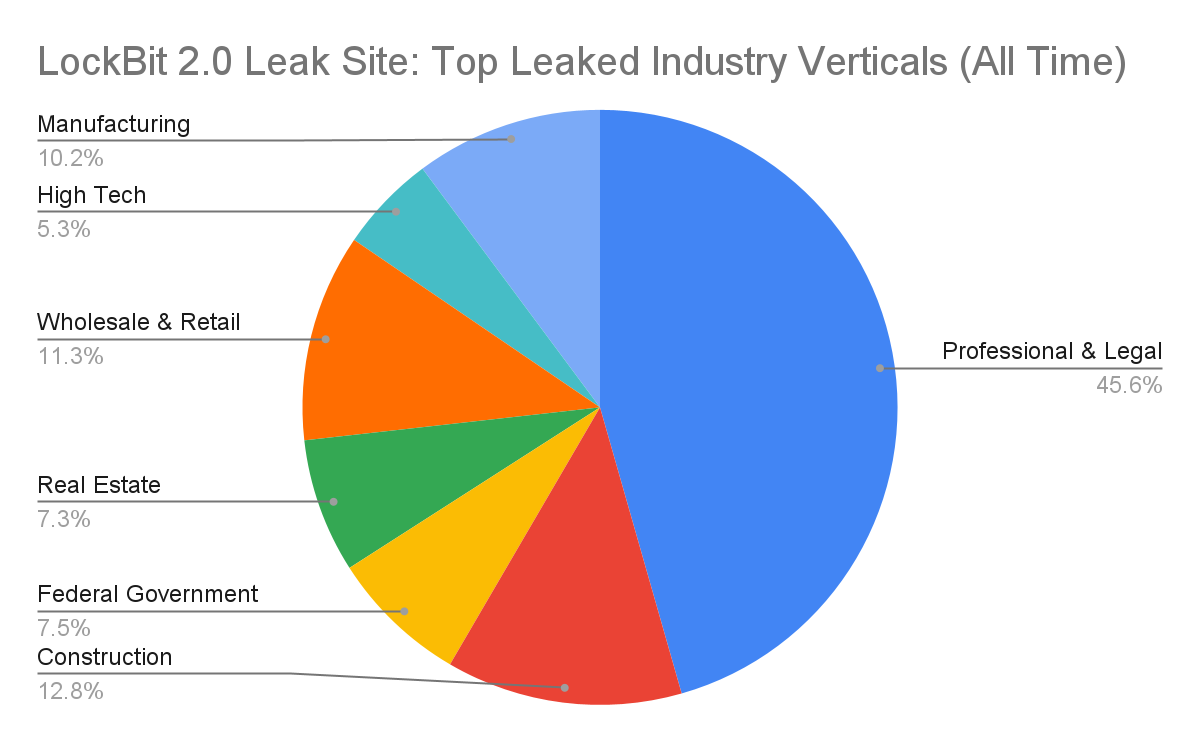
That's the share of ransomware leak site data attributed to LockBit 2.0, which persisted as the most impactful and the most deployed ransomware variant for the first quarter of 2022, according to Unit 42, followed by Conti, BlackCat, STORMOUS, and Hive, in the wake of Babuk, DarkSide and REvil's disappearance from the underground in 2021. Most impacted countries include the U.S., Italy, Germany, Canada, and France. That said, there are signs that REvil has returned from the dead.


