A new type of DDoS attack targets the cloud
The attack leveraged a zero-day flaw in the HTTP/2 protocol
A roundup of some of the noteworthy developments in the cybersecurity landscape, encompassing the latest vulnerability discoveries and emerging attack trends. Here are this edition’s top stories -
↘️ Amazon AWS, Cloudflare, and Google, revealed that a zero-day vulnerability in the HTTP/2 protocol (CVE-2023-44487) has been used by an unknown actor to fuel enormous, hyper-volumetric distributed denial-of-service (DDoS) attacks dubbed HTTP/2 Rapid Reset. The pioneering attacks, which represents an important evolution of the DDoS landscape, were detected in late August 2023. “For a sense of scale, this two-minute attack generated more requests than the total number of article views reported by Wikipedia during the entire month of September,” Google said. The power of the method is such that the August tsunami was launched using a modestly sized botnet — fewer than 20,000 machines, making it both potent and efficient. [The Hacker News / The Register / Bleeping Computer / WIRED]
↘️ The recent escalation of the Israel-Palestine conflict has been accompanied by numerous hacktivist groups taking sides to conduct a relentless wave of defacement and denial-of-service attacks against government websites, media outlets, and critical infrastructure. This includes AnonGhost, Anonymous Sudan, Indian Cyber Force, KillNet, Predatory Sparrow, SiegedSec, and ThreatSec, among others. The surge in hacktivism comes on the heels of the Red Cross issuing ethical guidelines for civilian hackers participating in armed conflicts, encouraging them to be more “humane.” [WIRED / The Record / Dark Reading / CyberScoop / SecurityScorecard / Check Point]

↘️ A recently identified phishing campaign is relying on LinkedIn smart links to bypass email defenses and deliver malicious lures into Microsoft users’ inboxes. Finance and manufacturing sectors were the most targeted. [Cofense]
↘️ The National Security Agency has published a repository of tools called ELITEWOLF to help critical infrastructure entities hunt for malicious activity in ICS and other OT environments. [GitHub]
↘️ A new report has revealed how the Israeli military uses mobile phone data from nearly 1.1 million residents of Gaza to track their movements via mobile phones and assess how many heeded Israel’s demand to evacuate the region and head south for their own safety. The development comes amid an escalation in the Israel-Palestine conflict, with Hamas leveraging hostages’ Facebook, Instagram, and WhatsApp accounts to livestream attacks and issue death threats. [The New York Times]
↘️ The collection of cybercriminal groups behind the infamous Magecart payment-card theft campaigns have come up with a previously unseen technique that involves using a website’s 404 error page to hide their credit card skimming code. [The Hacker News / Dark Reading]
↘️ Google is stepping up Google Play Protect’s security capabilities with real-time scanning at the code-level, which will trigger when installing an application that has never been scanned before, so as to ensure that the app is safe to install. The goal is to help detect emerging threats, protect users from polymorphic malware that rely on various techniques, including AI, to modify their features and avoid detection. [The Hacker News]
↘️ A rising trend in threat activity has been observed employing fake browser updates to disseminate malware. At least five distinct threat clusters — TA569 (aka SocGholish), RogueRaticate (FakeSG), ZPHP (SmartApeSG), ClearFake, and EtherHiding — have been tracked utilizing this deceptive tactic. In these attacks, fake browser update notices mimicking Chrome, Firefox, or Edge are served on compromised websites, luring users into downloading malicious software instead of legitimate updates. The success of these campaigns lies in exploiting users’ trust in known and safe sites. [The Hacker News / Krebs On Security]
↘️ In an internationally coordinated takedown, law enforcement agencies from nearly a dozen countries have taken over Ragnar Locker ransomware group’s online infrastructure, the latest in a string of efforts to clamp down on cybercrime and disrupt ransomware gangs. [The Hacker News]
↘️ Spyware products from the Intellexa alliance such as Predator have been found in at least 25 countries across Europe, Asia, the Middle East and Africa, indicating that they are being “traded on a near industrial scale and are free to operate in the shadows without oversight or any genuine accountability.” One of the key tools is Triton, a product that Intellexa has positioned as something that customers can use to infiltrate Samsung devices. In a related development, a short-lived spyware operation called Oospy, which emerged earlier this year after its predecessor Spyhide was hacked, has shut down. [The Hacker News / Dark Reading / TechCrunch]
↘️ A whopping 35 vulnerabilities affecting the Squid caching and forwarding web proxy remain unpatched two years after it was responsibly disclosed by security researcher Joshua Rogers to its developers. Part of a broader set of 55 flaws, a majority of the vulnerabilities can lead to a crash, but some can also be exploited for arbitrary code execution. [Joshua Rogers / The Register]
↘️ A new report finds that Telegram, a popular messaging app used by over 700 million people, continues to leak an individual’s IP address simply by adding a bad actor toe their contacts and accepting a phone call from them. The issue, which stems from a peer-to-peer connection between the two users, has been publicly known since September 2018. To avoid leaking your IP address, head to Telegram’s Settings > Privacy and Security > Calls, and then select “Never” in the Peer-to-Peer menu. [TechCrunch]
↘️ A lesser known threat actor known as Winter Vivern, likely operating with interests aligned to Belarus and Russia, has been observed exploiting a zero-day flaw in Roundcube Webmail servers with a malicious email campaign targeting governmental organizations. The fact that the group is now leveraging zero-day vulnerabilities marks an escalation and could be a harbinger of future activity, as it demonstrates a long-term interest in conducting espionage attacks against governmental organizations. [The Hacker News]
↘️ A group of academics has devised a novel side-channel attack dubbed iLeakage that exploits a weakness in the A- and M-series CPUs running on Apple iOS, iPadOS, and macOS devices, enabling the extraction of sensitive information from the Safari web browser. The disclosure comes amid the discovery of RowPress, a RowHammer technique to artificially induce bitflips at will in DRAM chips, and ultimately corrupt, modify, or steal sensitive data when a user-level application repeatedly accesses certain regions of DDR memory chips. [The Hacker News / The Register / Ars Technica / Dark Reading]
↘️ Threat actors are experimenting with lesser known attack vectors such as mDNS (multicast DNS) flood, CoAP (Constrained Application Protocol) flood, and ESP (Encapsulating Security Payload) flood to pull of distributed denial-of-service (DDoS) attacks. This follows a surge in hyper-volumetric HTTP DDoS (distributed denial of service) attacks, particularly using a newly disclosed exploit called HTTP/2 Rapid Reset. [The Hacker News]
↘️ The Nigerian Police Force arrested six suspects, aged from 19 to 27, and dismantled a mentoring hub linked to cybercrime activities, including business email compromise, identity theft, romance scams, and cyber fraud. [Dark Reading]
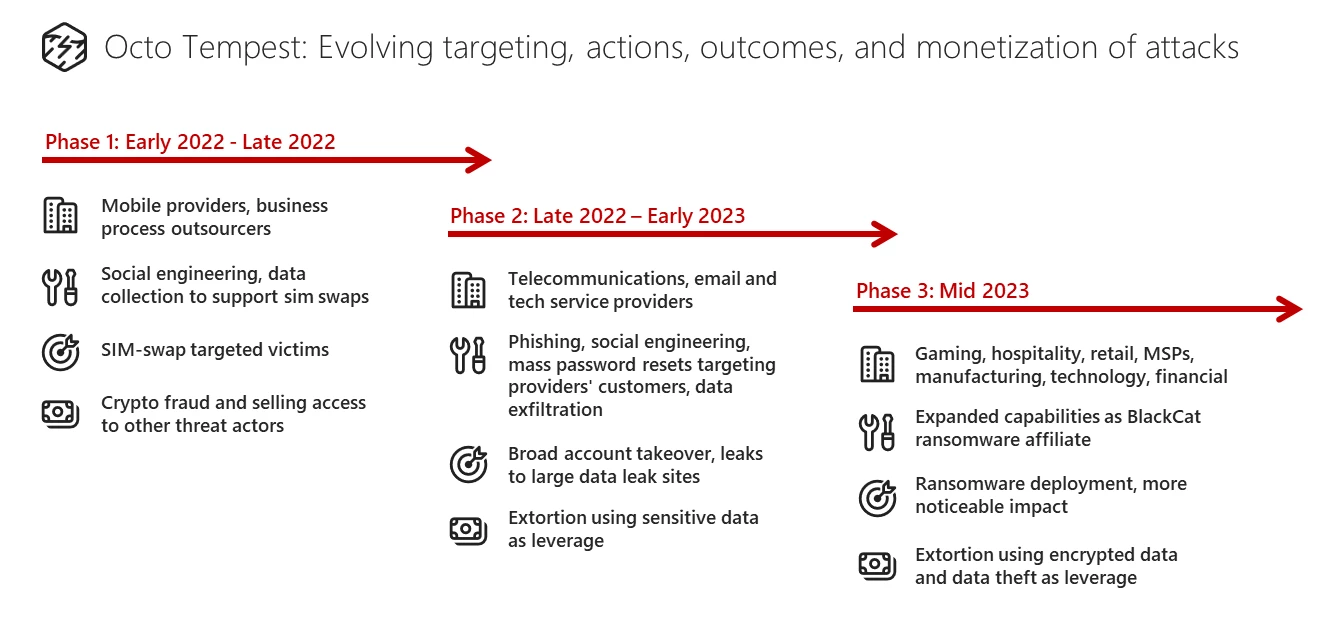
↘️ Microsoft laid out the myriad tactics and techniques adopted by a threat actor called Octo Tempest, also widely known as Scattered Spider, to pull off sophisticated social engineering campaigns and carry out cryptocurrency theft, data-leak extortion, and ransomware attacks. It marks one of the rare instances of Eastern European ransomware groups collaborating with native English-speaking criminals. The well-organized group has also been observed resorting to well-researched impersonations and violent threats to coerce high-profile targets into sharing data. Part of the threat actor’s success goes to their ability to study the organizations they attack and identify prime targets that can be impersonated in phone calls to IT help desks. [The Hacker News / CyberScoop / The Register]
↘️ The Five Eyes countries’ intelligence agencies jointly accused China of intellectual property theft and using artificial intelligence for hacking and spying against the nations. [Reuters]
↘️ APT28, a hacking group associated with Russia’s military intelligence agency, has been spying on French universities, businesses, think tanks, and government agencies since the second half of 2021 to obtain sensitive data by leveraging phishing attacks and zero-day security flaws. [ANSSI]
↘️ Personally identifiable information (PII) records, including Aadhaar cards, allegedly belonging to 815 million Indian residents have been being offered for sale on cybercrime forums for $80,000. [Resecurity]
↘️ New findings show that the site engagement feature in Google Chrome and Chromium-based browsers can leak the most frequented websites on the device by abusing a security feature called Lookalike Warnings, which notify users when they attempt to visit a website with a misspelled domain name (e.g., g0ogle.com instead of google.com). [Fingerprint]
↘️ The U.S. Securities and Exchange Commission (SEC) sued SolarWinds and Chief Information Security Officer Timothy Brown, alleging that the company concealed security failures since at least October 2018 that led to a massive cyber attack launched by Russian hackers that came to light in December 2020. SolarWinds, in response, accused the SEC of launching a “misguided and improper enforcement action” against the company and that it will “vigorously oppose this action.” [SEC / SolarWinds]
↘️ The U.S. government and a coalition of foreign allies as part of the International Counter Ransomware Initiative have pledged never to pay ransom demands in a bid to discourage financially motivated hackers and ransomware gangs profiting from cyber attacks. The willingness to pay might seem like an easy way out, but it introduces new risks in that there is no guarantee paying up will ensure the safe return of stolen data. What's more, companies that have paid ransoms are more likely to be hit again. [Reuters / TechCrunch / The Record]
↘️ The Russian government plans to have its own analogous version of the malware scanning platform VirusTotal up and running within the next two years, due to concerns the U.S. government could access data from the popular Google-owned service. [The Record]
↘️ Hackers are targeting accounts on Kodex, a platform that connects law enforcement agencies and tech companies and which is designed to verify emergency requests for customer data. [404 Media]
↘️ An Iranian threat actor named Scarred Manticore has targeted the high-profile sectors in the Middle East as part of efforts to collect intelligence. The quiet but sustained campaign is seen as a counteroffensive to rivals like Israel and a sign of the fast improving capabilities of Iranian hacking groups. [The New York Times / The Hacker News]
↘️ A thriving link-shortening service from a threat actor named Prolific Puma is providing attackers and scammers with thousands of domains in the past 18 months, helping them make their phishing and malware campaigns just a bit less detectable. The key to Prolific Puma’s operation is what’s called the “registered” domain generation algorithm, or RGDA, in which the domains created by the adversary are all properly registered and strategically aged to fly under the radar and make the command-and-control (C2) infrastructure more robust and fault tolerant. [The Hacker News]
↘️ An ongoing and coordinated campaign has been observed flooding the NuGet package manager with bogus packages that deploy malware with hidden code execution capabilities. Threat actors increasingly are recognizing the value of weaponizing open source packages as a way to target the software supply chain and thus reach an enormous target base with significantly less effort than other types of attacks can require. Needless to say, malware distribution through open-source packages is an ongoing threat. [The Hacker News]


