Apple's child abuse-privacy tightrope
The iPhone maker's plans to detect child sexual abuse imagery triggers debate
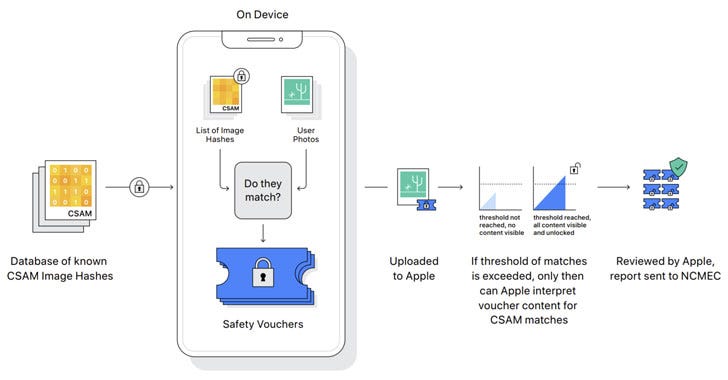
Apple is deploying a new privacy-preserving cryptographic system within iOS, macOS, watchOS, and iMessage that will allow it to detect potential child abuse imagery stored in iCloud Photos, in a radical move that has been branded as a “slippery slope” by security experts.
The child safety proposals are set to be rolled out in the U.S. in the coming months, and is expected to be introduced on a country-by-country basis after conducting a legal evaluation, although it has yet to provide a timeframe for such an expansion.
The initiative has come at a time when tech companies are facing mounting pressure from governments around the world to allow access to encrypted content, including messages, photos and videos, and even trace the source of unlawful messages, effectively breaking end-to-end encryption.

Viewed in that light, the new measures are part of the company’s attempt to strike a compromise between protecting customers’ privacy and meeting demands from law enforcement agencies in investigations pertaining to terrorism and child pornography — and by extension offer a solution to the so-called “going dark” problem of criminals taking advantage of encryption protections to cloak their contraband activities.
The development also marks a significant policy shift from a company that famously said “what happens on your iPhone, stays on your iPhone” and has turned privacy into a business advantage, with CEO Tim Cook in 2019 addressing the “chilling effect of digital surveillance,” noting that “in a world without digital privacy, even if you have done nothing wrong other than think differently, you begin to censor yourself.”
Apple isn’t unique in its efforts to combat of child sexual abuse imagery. Tech giants like Google, Facebook, Microsoft, Dropbox, and other cloud service providers already employ similar methods to identify illegal content on its services. But what makes Apple’s new system distinct is that the search begins on the user’s device, and not in the cloud.
A dangerous precedent?
The company’s privacy guarantees notwithstanding — the system doesn’t scan actual images on the devices, instead only comparing unique randomized strings of characters derived from those image files (aka hashes) — questions are being raised about how the tool could potentially repurposed or weaponized in the future to “scan for anything.”
While the detection is expected to leverage on-device machine learning techniques and only when iCloud photo sharing is enabled, the plans have sparked concerns that the iPhone maker could eventually be forced to enable monitoring of non-CSAM images, and in the process open the door for broader abuses by authoritarian regimes to spy on their citizens, since a system designed to detect one type of imagery could be broadened to other types of content, like terrorism or other forms of content perceived as anti-government or illegal.
“Now that this is possible to have access, authorities will push for more access,” Avast Chief Privacy Officer, Shane McNamee, said. “It’s like we’re peeking over your shoulder, but we’re wearing sunglasses and saying the sunglasses can only see bad things. And you have this little snooper on the device that’s just reading everything and checking it, not sending it to Apple unless you’re doing something wrong. That’s the problem — the definition of ‘doing something wrong’ could be broadened.”
Apple, however, has dismissed such criticisms, saying that safeguards are in place to prevent abuse of the system and that it would reject any demands put forth by different governments. “We will inform them that we did not build the thing they’re thinking of,” Erik Neuenschwander, Apple’s chief privacy engineer, said.
“Apple sells iPhones without FaceTime in Saudi Arabia, because local regulation prohibits encrypted phone calls. That’s just one example of many where Apple’s bent to local pressure. What happens when local regulations in Saudi Arabia mandate that messages be scanned not for child sexual abuse, but for homosexuality or for offenses against the monarchy?,” tweeted security and privacy expert Dr. Nadim Kobeissi.
Earlier this May, the New York Times revealed how Apple’s privacy and security concessions have “made it nearly impossible for the company to stop the Chinese government from gaining access to the emails, photos, documents, contacts and locations of millions of Chinese residents,” underscoring a pattern of giving in to the demands of the government in order to continue its operations in the country.
While doubtless well-intentioned, Apple’s new effort will not only likely redouble pressure from governments to get the company to comply with surveillance requests, but also give voice to a long-standing argument against the use of end-to-end encryption in messaging platforms, which render tools to detect child abuse images and in private messages useless, and compel services like Signal, WhatsApp, and Telegram to follow suit with similar technologies.
“Apple’s compromise on end-to-end encryption may appease government agencies in the U.S. and abroad, but it is a shocking about-face for users who have relied on the company’s leadership in privacy and security,” the Electronic Frontier Foundation (EFF) said, adding “even a thoroughly documented, carefully thought-out, and narrowly-scoped backdoor is still a backdoor.”
What’s more, no fewer than 7,000 individuals and organizations have signed an open letter calling on Apple to halt the implementation of its proposed content monitoring technology, stating that “the type of technology that Apple is proposing for its child protection measures depends on an expandable infrastructure that can’t be monitored or technically limited.”







What’s trending in security?
🇮🇱 Israeli government officials visited the offices of the hacking company NSO Group on Wednesday to investigate allegations that the firm’s spyware has been used to target activists, politicians, business executives, and journalists. In a related development, NPR also reported that the company has temporarily blocked several government clients globally from using its technology as the company probes their possible misuse. [MIT Technology Review / NPR]
🇮🇷 A cyber attack that derailed websites of Iran’s transport ministry and its national railway system in early July, causing widespread disruptions in train services, was the result of a never-before-seen reusable wiper malware called "Meteor." The campaign was dubbed MeteorExpress by researchers from SentinelOne. [The Hacker News]
🇨🇳 Researchers uncovered three-way cyber attack by Chinese military threat actors against Southeast Asian telcos since 2017 to “to facilitate cyber espionage by collecting sensitive information, compromising high-profile business assets such as the billing servers that contain Call Detail Record (CDR) data, as well as key network components such as the Domain Controllers, Web Servers and Microsoft Exchange servers.” [The Hacker News]
🔝 Intelligence agencies in Australia, the U.K., and the U.S. issued a joint advisory on Wednesday detailing the top 30 most exploited vulnerabilities in 2020 and 2021. [The Hacker News]
🚫 Researchers found a bug in Cobalt Strike, the pentesting platform used in red-team engagements. The attack vector basically worked by registering fake beacons, that the Cobalt Strike server then interacts with, and sending fake task replies from said beacon to the server, thus “squeezing out every bit of available memory” and triggering a denial-of-service condition. [SentinelOne]
⚠️ Google Play Protect, Android’s built-in malware detection and defense system, identified only 68.8% of more than 20,000 malicious apps, ranking last out of 15 security apps. “9 of the 15 apps achieved the top score in the endurance test. They came from Avast, AVG, Bitdefender, F-Secure, G DATA, Kaspersky, McAfee, NortonLifeLock und Trend Micro. This was followed by the apps from Avira, Protected.net, securiON and AhnLab, with 17.8 to 17.1 points. Ikarus managed to achieve 16 points, and the Google Service earned a mere 6 points,” the researchers noted. [AV-TEST]
🕸️ An Iranian cyber espionage group dubbed “Tortoiseshell” masqueraded as an aerobics instructor on Facebook in an attempt to infect the machine of an employee of an aerospace defense contractor with malware as part of a years-long social engineering and targeted malware campaign. “This campaign exemplifies the persistent nature of certain state aligned threats and the human engagement they are willing to conduct in support of espionage operations,” Proofpoint researchers said in a report. [The Hacker News]
🔐 Microsoft has begun testing a new feature in Edge browser called “Super Duper Secure Mode” to intentionally disable an important performance and optimization feature named support for JIT (Just-In-Time) compilation inside V8 JavaScript engine in order to enable more advanced security upgrades such as Controlflow-Enforcement Technology (CET) and Arbitrary Code Guard (ACG). [The Record]
ℹ️ Following Apple’s advances into consumer privacy with initiatives like App Tracking Transparency and App Store privacy labels, Google has shared more details about its upcoming safety section for apps in Google Play App Store, letting developers offer users a deeper insight into their apps’ privacy and security practices (like encryption), as well as explain the data may be collected and why prior to installation. The feature is expected to go live in Q1 2022. [Android Developers]
💲 In an interview with The Record, a new ransomware group named BlackMatter that specifically targets companies with revenues of more than $100 million said it will avoid certain industries like healthcare, adding it’s learning from the mistakes of other ransomware groups. [The Record]
🛡️ The U.S. Department of Homeland Security (DHS) unveiled the Joint Cyber Defense Collaborative (JCDC) to combat ransomware and cyberattacks, in partnership with Crowdstrike, Palo Alto Networks, FireEye, Amazon Web Services, Google, Microsoft, AT&T, Verizon, and Lumen in the wake of a string of high-profile attacks. The development comes as the frequency and severity of such attacks have increased in recent months, especially as ransomware developers and affiliates band together to make the attacks more lucrative. [The Wall Street Journal / Dark Reading]
🚨 Raccoon Stealer has been upgraded by its developer in order to steal cryptocurrency alongside financial information. [Sophos]
🔍 PunkSpider, a controversial search engine that crawls the web for vulnerable websites, has made a return a decade after it was first conceived. [WIRED]
🗃 The last two weeks in Northern Ireland’s Department of Health, Electronic Arts, ERG, GIGABYTE, Estonia’s Information System Authority, Italy's Lazio region, LINE, and UC San Diego Health.
304.7 million
That’s the total number of attempted ransomware attacks in the first half of 2021, out of which a record 78.4 million intrusions were detected in the month of June alone. The figure also surpasses the total number of attempted ransomware attacks detected for the whole of 2020, according to a new report published by SonicWall.
Tips, Comments, Ideas?
Send them my way by writing replying to this email.
Thanks again for reading. See you in the next edition!