Criminal marketplace Genesis goes down
Law enforcement agencies ramp up efforts to combat cybercrime
More than a dozen law enforcement agencies across the world teamed up to shut down Genesis Market, a notorious online black-market shop which specialized in the sales of account credentials for various services, device fingerprints, and cookies. According to Europol, 119 of the site’s users have been arrested. It’s believed to be located in Russia and launched in 2018 as an invitation-only marketplace.
The data was collected in real-time by leveraging various stealer malware families as initial access vectors to ultimately plant JavaScript code to grab all the relevant data. Other actors could then access stolen device fingerprints through the purchase of bots (i.e., the credential-harvesting malware) controlling the hacked machines to carry out identity theft or commit more attacks. The price varied based on the stolen data.

So long as the operators could still reach a victim’s devices, it could offer up-to-date data from that victim, making it a valuable resource for hackers to get hold of cookies and fingerprints to bypass two-factor authentication protections and anti-fraud detection systems. The seizure is just the latest in a wave of aggressive government operations targeting the infrastructure supporting the cybercrime ecosystem.
Disrupting darknet markets that sell stolen data and hacking tools has become a major focus of law enforcement agencies in recent years, along with the takedown of illegal cryptocurrency operations or exchanges that serve as money laundering hubs for stolen digital assets. While these takedowns and disruptions sometimes result in arrests and short-term problems for the users who have to find another platform to buy and sell stolen information, there is always another marketplace ready to fill the void.
What’s trending in security?
🔽 Microsoft, Fortra, H-ISAC partnered to take down illegal infrastructure used to host stolen and cracked copies of Cobalt Strike. The move is meant to prevent threat actors from being able to misuse the tool as part of their operations, something that has become commonplace in recent years. The tactic of going after the distribution of illicit copies of the software tool is a shift from past disruption efforts that targeted malware hackers command-and-control centers. [The Hacker News]
💥 A shadowy spyware vendor named QuaDream’s hacking tools have been used on journalists, political figures, and a civil-society worker, it has emerged. QuaDream has allegedly kept a very low profile, even lacking a website and social media presence. Its operations have been shrouded in mystery and only came to the forefront in recent years. It markets a surveillance platform called REIGN that functions as a “suite of exploits, malware, and infrastructure designed to exfiltrate data from mobile devices.” In a bid to evade export controls and oversight, the company sells its products outside of Israel through a Cyprus-based subsidiary called InReach. The malware used in the 2021 campaign, dubbed KingsPawn by Microsoft, is said to be delivered as part of the Reign platform, although there is no concrete evidence to support the claim at this stage. It also leveraged a then zero-day flaw in iOS 14 (called ENDOFDAYS) to deploy the espionage tool. While Apple has addressed the loophole, it is highly likely that the malware has been updated to account for newer versions. [The Hacker News / SC Magazine]
📧 The Dutch Police is sending emails to former RaidForums members, asking them to delete stolen data and stop illegal cyber activities and warning that they are not anonymous. The illegal marketplace was taken down in April 2022 in an international law enforcement operation. [Politie]
💣 DDoS attacks have once again moved to the forefront in recent years, in part owing to them being used as a cyber weapon of choice by various threat actors and hacktivist groups since the onset of Russia’s invasion of Ukraine in February 2022. The alarming frequency of DDoS attacks aside, large scale volumetric attacks — attacks above 100 Gbps — increased by 6% QoQ in the first quarter of 2023. Such attacks are also now relying on breached Virtual Private Servers (VPS). Ransom DDoS attacks, which are carried out to extort ransom payments, stood at 16%. Some of the top targeted countries include Israel, the U.S., Canada, China, and Singapore. Netscout, in its threat intelligence report for H2 2022, listed TCP ACK, TCP SYN, and DNS amplication as the top DDoS attack vectors. [Cloudflare / Netscout]
↘️ The U.S. Federal Bureau of Investigation is warning that criminal actors are posing as Chinese law enforcement officials or prosecutors in financial fraud schemes targeting Chinese communities in the country. [FBI]
⚠️ A new cloud attack leveraged a security vulnerability in Log4j to install a proxyware service and turn it into a proxy server. This allowed the attacker to “sell the IP to a proxyware service and collect the profit,” researchers said. The scheme, called proxyjacking, shares characteristics of cryptojacking in that both profit off the bandwidth of a victim. [Sysdig]
💸 Coinbase wallet and other decentralized crypto apps (dapps) have been found to be vulnerable to “red pill attacks,” a method that can be used to hide malicious smart contract behavior from security features. Coinbase has since addressed the reported security problems. In a related development, researchers detailed a novel attack against Elliptic Curve Digital Signature Algorithm (ECDSA) to break into 773 unique crypto wallets. [ZenGo / Kudelski Security]
⛔ Amazon banned the sale of Flipper Zero, a $169 portable security penetration testing tool for wireless devices, tagging the product as a card-skimming device. [Bleeping Computer]
📱 Security researchers have found that rogue versions of Pinduoduo’s now-suspended Android app leveraged about 50 flaws in the operating system to escalate privileges, download and execute additional malicious modules, access users’ data, prevent itself from being uninstalled, and eavesdrop on rival apps by tracking user activity on their apps. “The app deployed a method that allowed it to push updates without an app store review process meant to detect malicious applications,” CNN earlier this month. The findings are also a violation of China’s data privacy legislation, which went into effect in 2021. One of the flaws in question is CVE-2023-20963. [The Hacker News]
🧠 OpenAI’s ChatGPT may be facing privacy and regulatory woes for building its AI model using “publicly available personal information,” but it has also patched multiple severe vulnerabilities that could have allowed attackers to take over user accounts and view chat histories. Threat actors, in the meanwhile, are also exploiting its rising popularity to spread malware hosted on Google Drive, Trello, and fraudulent sites via compromised Facebook accounts. Also observed are sponsored ads offering ChatGPT and Google Bard on these hijacked accounts to distribute the RedLine Stealer. The commodity malware is an inspired choice for the campaign considering it costs only $100 to $150 to buy it on the darknet, which gives attackers a significant return on investment (ROI) for their cybercriminal activity.
This adds to growing concerns that that tools that make use of large language models (LLM) could dramatically lower the bar to write steganographic and polymorphic malware. However, it also bears noting that such attacks are not inherently new and threat actors will always find ways to abuse technology to their advantage. The use of AI, in that light, is just the latest twist in the cat-and-mouse game between attackers and defenders. [CloudSEK / Forcepoint / SentinelOne / SecurityWeek]
👻 Hacktivist groups like GhostSec are setting their eyes on Global Navigation Satellite System (GNSS) receivers. Attacks on such systems could have severe consequences, including loss of positioning, disruptions, and other safety risks. [Cyble]
☢️ Chinese companies in the nuclear energy sector are the target of a new phishing campaign orchestrated by a group called Bitter APT. The attacks culminate in the deployment of payloads that are responsible for establishing persistence and downloading further malware. Attacks orchestrated by Bitter, also known as APT-C-08, APT-Q-37, or Manlinghua, have targeted China, Pakistan, Saudi Arabia, and Bangladesh in the past. [Intezer / ASEC]
🔒 Researchers have discovered a new custom ransomware strain called Rorschach (aka BabLock) that’s believed to have been active since June 2022. Besides being the fastest-ever ransomware, it also includes safeguards to prevent analysis and boasts of a self-replicating ability when executed on a Domain Controller, raising the bar for file-encrypting attacks. [The Hacker News]
🕸️ An estimated one million WordPress websites have been infected over the past six years in a long-lasting malicious campaign called Balada Injector, often quickly co-opting newly disclosed flaws in themes and plugins to drop backdoors on the compromised hosts. [The Hacker News]
⬆️ Google is upping the privacy ante for its Play Store with new rules that mandate Android app developers provide straightforward options for users to delete accounts and associated data. [The Hacker News]
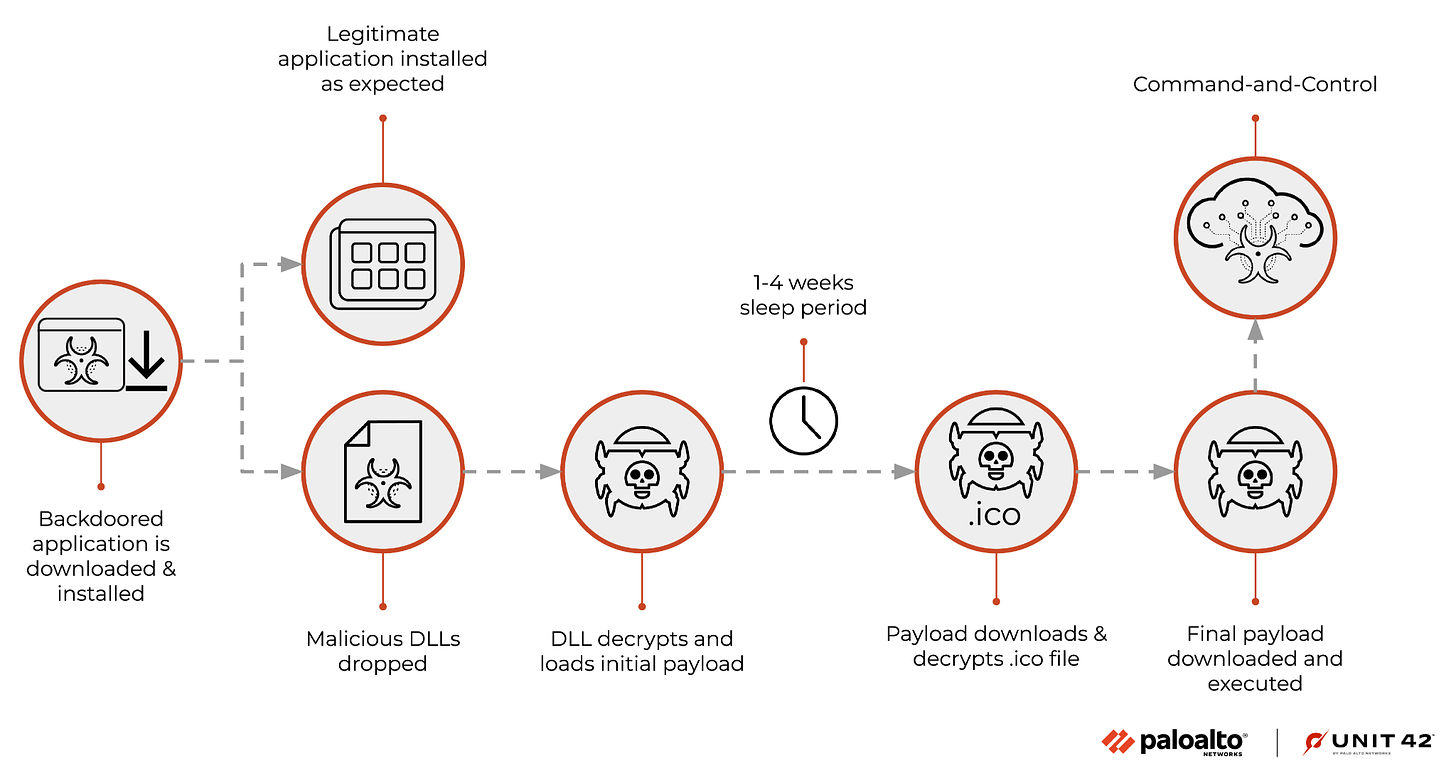
🚨 Security researchers have sounded the alarm on what’s another major SolarWinds or Kaseya-like supply chain attack, this time involving Windows and Mac versions of a widely used video conferencing, PBX, and business communication app from 3CX. The intrusion has been pinned on the North Korea-linked Lazarus Group as part of a campaign designed to target the company’s downstream customers and infect select cryptocurrency companies with a backdoor called Gopuram. It’s believed that the operation was detected in its initial stages, before it reached the magnitude of the SolarWinds incident that came to light in December 2020. [The Hacker News / Dark Reading]
🚩 A pro-Islamic group that has hit numerous targets in France, Germany, the Netherlands, Sweden, and Australia with distributed denial-of-service (DDoS) attacks over the past few months may actually be a subgroup of the Russian hacktivist collective known as Killnet. [Trustwave]
⏬ Over 15 million publicly facing services are susceptible to at least one of the 896 vulnerabilities listed in CISA’s Known Exploitable Vulnerabilities (KEV) catalog. [Rezilion / CISA]
🔍 The Indian government is considering procuring spyware from “less exposed competitors to the NSO Group” in the wake continued spotlight against the company’s Pegasus surveillance software. Although India has not publicly acknowledged being a customer of NSO, Pegasus has been found on the phones of Indian journalists, lawyers, and activists. On a related note, an unknown federal agency in the U.S. used a front company named Cleopatra Holdings to procure a location tracking tool from NSO Group known as Landmark, days after the controversial spyware vendor was blocklisted by the government in November 2021. [The Financial Times / The New York Times]
👁️ Two highly targeted campaigns that took place in late 2022 involved several zero-day exploits for Android, iOS and mobile versions of the Chrome browser to infect devices with spyware. Amnesty said the exploit is “developed by a commercial cyber surveillance company and sold to governments hackers to carry out targeted spyware attacks.” [The Hacker News / The Record]
🦊 A fast-evolving toolkit called AlienFox can be used to compromise misconfigured web hosting services to harvest sensitive information like API keys and other secrets, marking a fresh twist in opportunistic cloud attacks. [The Hacker News]
⛽ A pro-Russia hacktivist group known as Zarya claims to have breached the network of an unnamed Canadian gas pipeline company in February and caused damage that resulted in loss of profits. [Kim Zetter]
🪲 Google is calling on vendors to provide more transparency into their vulnerability management practices. Vulnerabilities pose great risks not only as zero-days, but also if they remain unpatched, weakening both enterprise and end-user security posture. [The Hacker News / SecurityWeek / CyberScoop]
🏫 The Pakistan-aligned Transparent Tribe has been experimenting with new ways to target educational institutions in India. While not very sophisticated, the actor has continuously changed its operational strategy, expanding its victimology beyond the defense sector to target educational institutions and students. [The Hacker News]
🔊 A novel attack method called Near-Ultrasound Inaudible Trojan (NUIT) has been found to exploit vulnerabilities in microphones and voice assistants to silently and remotely access smart phones and other connected home devices. “NUIT appears as a sound clip in near-ultrasound frequency range (16kHz-20kHz), thus can be played on the victim’s COTS speaker to attack the voice assistant (i) on the same device;[and] (ii) on victim’s other devices,” researchers behind the study said. [NUIT Attack]
🐍 A new Python-based Legion malware called Legion that’s capable of harvesting credentials is being offered for sale on Telegram. It’s also promoted on YouTube through tutorial videos, suggesting that it is widely distributed and likely paid malware. The use of Telegram for peddling the tool should not come as a surprise, as the messaging platform has emerged as a hotbed for illegal activities, including leveraging it to automate phishing attacks. [The Hacker News]
🔢 The Indian government revealed late last month that a total of 13,91,457 cybersecurity incidents were reported to the Indian Computer Emergency Response Team (CERT-In) in 2022. Out of this staggering number, only 15 entities reported the incidents to the cybersecurity agency within the 6-hour timeline. [MediaNama]
🚘 A hacking device that’s sold for up to €5,000 can allow thieves to perpetrate keyless car theft and steal a wide range of car models using an attack method named CAN injection. “The way CAN Injection works is to get into the car's internal communication (i.e. the CAN bus) and inject fake messages as if from the smart key receiver, essentially messages saying ‘Key validated, unlock immobilizer,’” Canis Automotive Labs CTO Ken Tindell said. “In most cars on the road today, these internal messages aren’t protected: the receivers simply trust them.” [Canis Automotive Labs]
🏫 The Transparent Tribe threat actor has been attributed to a set of weaponized Microsoft Office documents in intrusions directed against the Indian education sector to deploy a continuously maintained piece of malware called Crimson RAT. The actor also shares overlaps with another group known as SideCopy, so named for emulating the infection chains associated with the SideWinder group. SideWinder is a suspected Indian threat actor with similarities to the DoNot Team. [The Hacker News]
🌐 A newly disclosed security flaw in the LibreNMS open source network monitoring solution (affecting versions 22.10.0 and prior) could be exploited by an unauthenticated attacker to gain remote code execution. [Sonar]
💶 An emerging European malware-as-a-service (MaaS) operator called FusionCore has been observed peddling a wide range of malware such as information stealers, crypters, and ransomware, underlining the new trend of cyber threats evolving into profitable criminal enterprises. [Cyfirma]