Is this the end of the road for LockBit?
The LockBit ransomware operation was taken down in a law enforcement operation last month
↘️ Illicit addresses sent $22.2 billion worth of cryptocurrency to services in 2023, down from $31.5 billion sent in 2022, with a majority of funds routed to DeFi protocols and centralized exchanges. What’s more, administrators and sellers on dark web marketplaces pulled in an estimated $1.7 billion in cryptocurrency-based revenues. Another notable shift is the threat actors’ use of cross-chain bridges for money laundering purposes. North Korean threat actors like the Lazarus Group have shifted to a new mixer called YoMix following Sinbad’s takedown, witnessing a 5x surge during the year. “Roughly one third of all YoMix inflows have come from wallets associated with crypto hacks,” Chainalysis said. “The growth of YoMix and its embrace by Lazarus Group is a prime example of sophisticated actors’ ability to adapt and find replacement obfuscation services when previously popular ones are shut down.” [Chainalysis]
↘️ A Chinese-speaking threat actor called GoldFactory is using a novel mobile banking trojan targeting Android and iOS that targets users in Thailand and Vietnam with an aim to steal facial recognition data and using it to access bank accounts. Victims who download the malicious apps are prompted to record a video for facial recognition purposes, which is “then used as raw material for the creation of deepfake videos facilitated by face-swapping artificial intelligence services.” The latest development seeks to undermine security measures imposed by the banking sector in Thailand that requires users to confirm larger transactions using facial recognition to prevent fraud. The distribution strategy adopted by the operators to target iOS users stands out. Initially leveraging Apple's mobile application testing platform, TestFlight, the modus operandi has shifted to persuading the victims to install a Mobile Device Management (MDM) profile post removal of their malicious app from the platform. [The Hacker News / The Register]

↘️ Multiple hacking groups like SiegedSec and ByteMeCrew have exploited a security flaw in a spyware solution called TheTruthSpy that existed since February 2022 to harvest data from thousands of Android devices. It comes as cybercriminals associated with off-the-shelf spyware are bypassing Apple’s security checks by offering apps containing an embedded custom keyboard that are distributed via the TestFlight program to spy on people’s iPhone activity. These keylogger services are offered for cheap as $30. Consumer-grade phone-monitoring apps continue to be marketed, even as several others such as PhoneSpector, Highster, Retina-X, SpyFone, and SpyTrac have shuttered in the wake of increased scrutiny. Last month, 404 Media — building off prior research from Irish Council for Civil Liberties (ICCL) in November 2023 — unmasked the connections between Patternz and Nuviad. [TechCrunch / Certo / 404 Media]
↘️ Mozilla’s latest *Privacy Not Included report delved into the world of romantic AI chatbots, and perhaps nor surprisingly, as many as 11 of them were found to be bad for user privacy, collecting vast troves of personal information and at the same time carrying little to no information about how they worked. These apps had an average of 2,663 trackers per minute, with Romantic AI incorporating 24,354 trackers in one minute. Even worse, most of them use that data to serve ads and some don’t even have an option to delete the data you have shared with them. They also lack information about how they manage security vulnerabilities and whether they use encryption. [Mozilla]
↘️ Smart home security camera maker Wyze informed users of a glitch that allowed about 13,000 users to potentially see other people's camera feeds. Of these 13,000 users, the company said 1,504 users actually looked at the feeds of others. “The incident was caused by a third-party caching client library that was recently integrated into our system,” the said. “This client library received unprecedented load conditions caused by devices coming back online all at once. As a result of increased demand, it mixed up device ID and user ID mapping and connected some data to incorrect accounts.” Last year, Wyze webcams suffered from a similar web caching issue that made it possible to view other people’s homes. [Wyze / The Verge]
↘️ In a groundbreaking operation, a coalition of international law enforcement operation has dismantled the notorious LockBit ransomware gang, seizing the group’s darknet websites, source code, as well as a wealth of intelligence on the group’s activities and affiliates. The breadth of the takedown itself is multifaceted and impacts everything from LockBit’s infrastructure backbone to the cryptocurrency accounts linked to the ransomware group. The effort, codenamed Operation Cronos, has led to arrests of two LockBit operators in Poland and Ukraine, with the U.S. Department of Justice (DoJ) unsealing indictments, charging Russian nationals Artur Sungatov and Ivan Kondratyev with deploying LockBit ransomware against U.S. victims. A prolific group operating since September 2019, LockBit is estimated to have breached over 2,000 victims and netted $120 million in illegal profits. That said, the exact impact of the takedown remains to be seen and if LockBit will spring up spring up with a new rebrand, as ransomware gangs are wont to do.
LockBit has since bounced back with a new dark web site and called for more attacks against the government sector, highlighting the whack-a-mole nature of the fight against ransomware. “I am very pleased that the FBI has cheered me up, energized me and made me get away from entertainment and spending money, it is very hard to sit at the computer with hundreds of millions of dollars, the only thing that motivates me to work is strong competitors and the FBI, there is a sporting interest and desire to compete,” LockBitSupp opined. The U.K. National Crime Agency (NCA), which led the takedown efforts, said LockBit remains “completely compromised” and that it continues to disrupt their operations. But the resurgence of BlackCat and LockBit is a sign that ransomware groups are staging quicker recoveries than before and that takedowns alone won’t solve the menace. [WIRED / The Hacker News / KrebsonSecurity / Ars Technica / The Guardian]
↘️ The U.S. government released new guidance on the actions that water and wastewater (WWS) sector entities should take to improve the resilience of their networks to cyber attacks. WWS entities are advised to reduce internet exposure by removing OT devices from the public access, conduct regular assessments to identify vulnerable OT and IT systems and prioritize patching, and improve password hygiene by changing default passwords to unique, complex ones and implementing multi-factor authentication (MFA). [CISA]
↘️ Apple is adding the quantum-computing resistant PQ3 protocol to iMessage as part of iOS 17.4, iPadOS 17.4, macOS 14.4, and watchOS 10.4 updates. Joining Apple is Tuta (formerly Tutanota), which has also released its own post-quantum encryption protocol called TutaCrypt to secure communications from powerful decryption attacks in the future. [The Hacker News / Dark Reading / Tuta]
↘️ The U.K.’s National Cyber Security Centre (NCSC) has warned small and medium-sized enterprises (SMEs) that they could be exposed to attacks targeting their private branch exchange (PBX) phone systems. “Attackers can find vulnerabilities by using scanners or by exploiting system weaknesses such as unchanged default passwords, open SIP ports, or incorrectly managed (or non-existent) firewalls,” NCSC said. “Once inside, criminals can route high-rate international or premium-rate numbers through the system.” [NCSC]
↘️ One of the main key leaders of the company behind the encrypted communication tool EncroChat has been extradited to France from the Dominican Republic. The unnamed person was arrested in the Dominican Republic in May 2022 and has been under house arrest since then. He is suspected, among other things, of illegally importing and selling illicit drugs, aggravated money laundering, illegal arms possession, and supplying or transferring a cryptologic device without integrity control or prior declaration to the authorities. EncroChat, an encrypted phone network that was used by organized crime groups, was disrupted by law enforcement in June 2023. [Eurojust]
↘️ A high-severity security vulnerability impacting Zyxel firewalls has been found to be less severe than previously thought. The flaw, tracked as CVE-2023-33012, was originally patched in July 2023, although details about it was only publicly disclosed last month. “It only affects a specific configuration, [and] is not easy to re-exploit,” security researcher Jacob Baines said. [VulnCheck]
↘️ The U.S. National Institute of Standards and Technology (NIST) has released version 2.0 of its Cybersecurity Framework (CSF) with an “expanded scope that goes beyond protecting critical infrastructure, such as hospitals and power plants, to all organizations in any sector.” CSF is a set of best practices and recommendations to help organizations improve their cybersecurity posture as well as understand, assess, prioritize, and communicate their cybersecurity efforts. [NIST]
↘️ A sprawling ad fraud campaign dubbed SubdoMailing is using over 8,000 domains and 13,000 subdomains belonging to well-known brands and institutions to send up to five million emails per day and generate revenue through scams and malvertising. The rampant activity has been attributed to a threat actor named ResurrecAds. [The Hacker News]
↘️ Researchers have found serious security flaws in cheap video door bells sold by a Chinese company called Eken under various brand names on Amazon, Shein, and other sites. Among the camera’s vulnerabilities are sending public IP addresses and Wi-Fi SSIDs (names) over the Internet without encryption, accessing still images from the video feed by knowing the camera’s serial number, and even taking control of the camera putting them into pairing mode and connecting through its companion mobile app Aiwit. In other news, Chinese PC maker Acemagic has admitted some of its products shipped with pre-installed malware such as Bladabindi (aka NjRAT) and RedLine Stealer. The company blamed it on software adjustments made by developers to reduce boot times “without obtaining software digital signatures.” The developments come as the U.S. launched a probe into possible security risks of Chinese-manufactured vehicles, saying modern cars are like smartphones and could be used for espionage by collecting sensitive data about citizens and infrastructure. [Consumer Reports / The Register / The White House]
↘️ Meta patched a critical vulnerability that could have been exploited to take control of any Facebook account by exploiting a bug in the password reset process that sends a unique six-digit unique authorization code to a different device the user is logged into. Further analysis found that not only was this code active for roughly two hours, it had no brute-force attack protection, thus allowing an attacker with knowledge of the targeted individual’s username to seize control of the account. The bug was patched by Meta on February 2, 2024, following responsible disclosure on January 30. [infosec writeups]
↘️ Law enforcement agencies in the U.S. are using push notifications to catch suspected kidnappers and pedophiles. In December 2023, it emerged that the push notification services operated by Apple and Google could be used to extract metadata information based on what’s called a push token, which can be used to identify users and are stored on the company’s servers. [The Washington Post]
↘️ The ALPHV/BlackCat gang has announced that mysteriously shut down the ransomware operation, claiming that it was the work of law enforcement. Speculations are abound that the shutdown is likely an exit scam, prompted by the gang leaders’ unwillingness to share a newly received $22 million ransom payment with an affiliates that carried out the attack against UnitedHealth’s Change Healthcare. The weakening of two notorious gangs that have caused so much disruption marks a significant milestone in efforts by governments to thwart cybercriminals. [WIRED / Krebs on Security / Ars Technica / The Hacker News / The Record]
↘️ Cybercrime victims in the U.S. lost a record $12.5 billion in 2023, a 22% increase from the previous year, led by investment scams. [FBI Internet Crime Complaint Center]
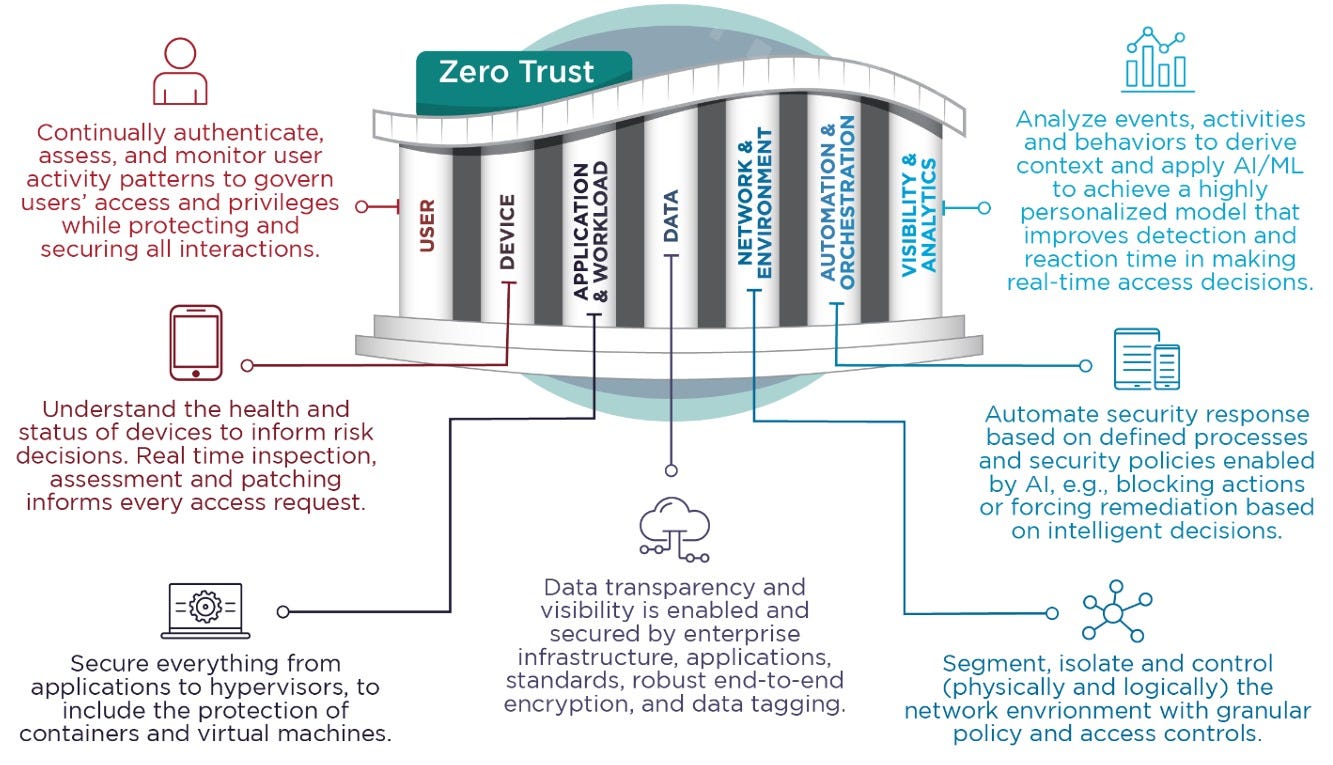
↘️ U.S. cybersecurity and intelligence agencies have released recommended best practices and/or mitigations to help organizations improve the security of their cloud environment(s). It also follows guidance from the National Security Agency (NSA) to limit an adversary’s lateral movement activities by adopting zero trust framework principles. [CISA / NSA]
↘️ Chinese company AnyCubic has shipped new Kobra 2 firmware to fix a zero-day vulnerability that was exploited last month to print security warnings on 3D printers worldwide. The unspecified vulnerability in the MQTT service made it possible to send arbitrary commands to an internet-connected printer. [Bleeping Computer / TechCrunch]
↘️ Multiple unpatched security flaws have been disclosed in Sciener firmware that could be exploited to manipulate Kontrol and Elock locks and unlock them. “These vulnerabilities allow attackers with physical, adjacent, or Bluetooth connection proximity to the lock access of various capabilities to compromise the lock integrity, without victim knowledge or interaction,” CERT/CC said. [Aleph Research / CERT/CC]
↘️ A concerted cyber compromise campaign is targeting cloud servers running misconfigured and vulnerable instances of Apache Hadoop, Atlassian Confluence, Docker, and Redis to drop a crypto mining tool and a Linux-based reverse shell that would allow potential future targeting and malware infestations. The attacks underscore the time and effort threat actors are putting into exploiting vulnerabilities in internet-facing services to gain initial access. [The Hacker News]
↘️ The sanctioned Tornado Cash mixer was compromised with malicious JavaScript code to target users accessing the service via IPFS gateways. “This code was designed to covertly capture and send users' private deposit notes to an unauthorized external server,” Checkmarx said. “Deposit notes in Tornado Cash act like private keys, crucial for accessing and managing funds within the service.” The compromise was detected by security researcher Gas404. [Gas404 / Checkmarx]
↘️ Researchers have found that hackers could easily leverage rogue Wi-Fi networks at Tesla charging stations to steal vehicles. The idea, in a nutshell, is to create a Wi-Fi network that spoofs a legitimate network found at Tesla service centers and broadcast the network via Flipper Zero (or Raspberry Pi or any device that comes with Wi-Fi hotspot capabilities). Should a victim connect to the network, they are served a bogus login page designed to steal their Tesla account credentials, thereby allowing the attackers to login to the Tesla app to track the car in real-time and even add a new phone key to unlock the vehicle. Making matters worse, Tesla owners are not notified when a new phone key is set up. [Gizmodo]
↘️ Developers accidentally leaked 12.8 million secrets on public GitHub repositories in 2023, a 28% jump from the previous year. What’s more, seven in 1000 commits, 4.6% of active repositories, and 11.7% of contributing authors exposed at least one secret last year. One particularly alarming trend is the 1212x surge in OpenAI API key leaks, leaking an average of 46,441 API keys per month, reflective of the explosive growth of AI technologies throughout the year. The development comes as it's becoming evident that repositories for machine learning models like Hugging Face are susceptible to the same kind of supply chain attacks that threat actors have executed successfully for years via npm, PyPI, and other open-source repos, and deliver malicious code into development environments. [GitGuardian]
↘️ An emerging international network of online groups like 764 and the Com spread across Discord, Roblox, and Telegram are targeting thousands of children to coerce them into self-harm and produce child sexual abuse material (CSAM). [The Washington Post / WIRED / FBI]
↘️ The threat actor known as UAC-0050, which has a track record of deploying Remcos RAT and other off-the-shelf malware against Ukraine, has been disclosed as likely linked to a Russia-based mercenary group called The DaVinci Group. “The domain 8161[.]uk is The DaVinci Group’s main website, whereby they advertise their services, such as hacking people’s email accounts, social media accounts, instant messaging accounts, remote access to PCs, launching Denial of Service (DoS) attacks, wiping files/evidence from other computers, and even they claim to have access to up to 150,000 CCTV cameras in Moscow,” security researcher Will Thomas said. [BushidoToken]