LastPass hackers stole customers' password vaults
Decoding LastPass' data breach notice and what it means
Password management firm LastPass disclosed the hackers behind an August data breach stole a massive stash of customer data, including reams of identifiable information and password vault data that could be exposed by brute-forcing or guessing master passwords. This is yet another reminder any password is only as strong as its strength and the encryption used to secure it. Users are advised to be extra alert for phishing emails and phone calls that aim to exploit their compromised personal data.
LastPass also reiterated that it would be extremely hard for the threat actors to brute-force the master passwords for customers following its password best practices. But here is the catch. The company began enforcing a twelve-character password only since 2018, meaning if you had a LastPass account before 2018, chances are that your master password doesn’t meet this requirement. This not only exposes users to a greater risk, but also lays the groundwork for shifting the blame on customers should the passwords be decrypted as a result.
What’s trending in security?
🚩 Microsoft said it allowed legitimate digital certificates to sign malware-laced drivers in the wild, effectively allowing multiple hacking groups to bypass security protections and kill processes associated with antivirus (AV) and endpoint detection and response (EDR) products. [The Hacker News / Ars Technica / WIRED / Decipher]
🔽 Web application firewalls from AWS, Cloudflare, F5, Imperva, and Palo Alto Networks could be subverted by a generic attack using the popular JavaScript Object Notation (JSON) format to obfuscate rogue database commands and escape detection. [The Hacker News]
🛡️ Google announced OSV-Scanner, a free scanner that open source developers can use to identify known vulnerabilities relevant to their projects and their transitive dependencies (i.e., code packages that are indirectly pulled into projects by other dependencies). The idea is to secure the software supply chain and alert developers about issues in third-party components. [The Hacker News]
⚠️ Facebook’s parent, Meta, agreed to pay $725 million to settle a lawsuit alleging the social media platform allowed millions of its users’ personal information to be accessed by third-parties without their consent. The settlement adds to a long list of fines and penalties that the company has paid in the wake of the Cambridge Analytica scandal and other privacy mishaps. [The Hacker News]
🔐 Researchers have developed a new method that enables users to search for information in a remote database privately, without revealing the information they are seeking to the server, that is about 30 times faster than other techniques. [MIT]
🚨 The U.S. Department of Justice (DOJ) seized four-dozen domains that sold booter or stresser services that make it easy for paying users to launch powerful Distributed Denial of Service (DDoS) attacks against a wide array of targets. It also charged six U.S. men with computer crimes related to their alleged ownership of the popular DDoS-for-hire services. [The Hacker News / Krebs on Security]
↘️ Threat actors can hijack and weaponize machine learning models to deploy malware and move laterally across enterprise networks, serving as a new launchpad for attacks that can poison an organization’s supply chain. A proof-of-concept (PoC) demonstrated that it’s possible to embed a ransomware executable into a model using a technique akin to steganography, causing it to be automatically launched when loading the PyTorch model. This technique could be exploited to conduct a supply chain attack by poisoning a service provider to distribute a trojanized model to all downstream users. [HiddenLayer]
💡 A new spotlight on the FIN7 Russian-speaking and financially motivated threat actor has revealed, among others, the group’s internal hierarchy and its use of an automated attack system that exploits Microsoft Exchange and SQL injection vulnerabilities to breach corporate networks, steal data, and select targets for ransomware attacks based on their financials. [The Hacker News]
🖥️ Microsoft detailed a bypass vulnerability in Apple’s Gatekeeper mechanism that could be exploited to execute malicious apps on macOS systems. Gatekeeper mitigates the threat of harmful apps that users might download from sketchy sites, but getting around this barrier could have serious security implications. [The Hacker News]
💲 An Android malware campaign dubbed MoneyMonger has been found hidden in money-lending apps developed using Flutter. The trend is emblematic of a rising tide of cybercriminals stealing personal information from victims and blackmailing them to extract money. [The Hacker News]
📶 U.S. intelligence agencies have released guidance on the security risks associated with 5G network slicing, potentially exposing users to a wide range of threat vectors: denial-of-service, jamming, identity theft, and adversary-in-the-middle attacks. This could hamper confidentiality, integrity, and the availability of network services. [National Security Agency]
🤖 The newly discovered Zerobot botnet continues to evolve, increasingly targeting connected devices with new exploits and distributed denial-of-service attack capabilities, expanding the malware’s reach to different types of Internet of Things (IoT) devices. “Zerobot is capable of propagating through brute-force attacks on vulnerable devices with insecure configurations that use default or weak credentials,” Microsoft said. [The Hacker News]
⬇️ Researchers have found that the Secret Network and PowerDVD are vulnerable to security compromises stemming from long delays in deploying updates to address known issues in Intel Software Guard Extensions (SGX), enabling extraction of cryptographic keys. [SGX.fail]
💵 The China-linked nation-state hacking group tracked as APT41 (aka Barium and Winnti) are estimated to have stolen at least $20 million in U.S. covid relief benefits, marking the first instance of pandemic fraud tied to foreign, state-sponsored cybercriminals publicly acknowledged by the U.S. government. [NBC News]
⛔ A new Python-based backdoor targeting VMware ESXi virtualization servers likely by exploiting known security defects (such as CVE-2019-5544 and CVE-2020-3992) for initial compromise. The implant enables threat actors to execute commands remotely on a compromised system. [Juniper Threat Labs]
🔎 The U.S. Federal Bureau of Investigation (FBI) is urging users to use ad blockers over warnings that “cyber criminals are using search engine advertisement services to impersonate brands and direct users to malicious sites that host ransomware and steal login credentials and other financial information.” [FBI]
🪙 South Korea’s National Intelligence Service (NIS) revealed that state-sponsored North Korean hackers had stolen $1.2 billion in cryptocurrency and other digital assets from targets around the world over the last five years. Roughly $626 million of the digital funds have been taken in 2022 alone. [Associated Press]
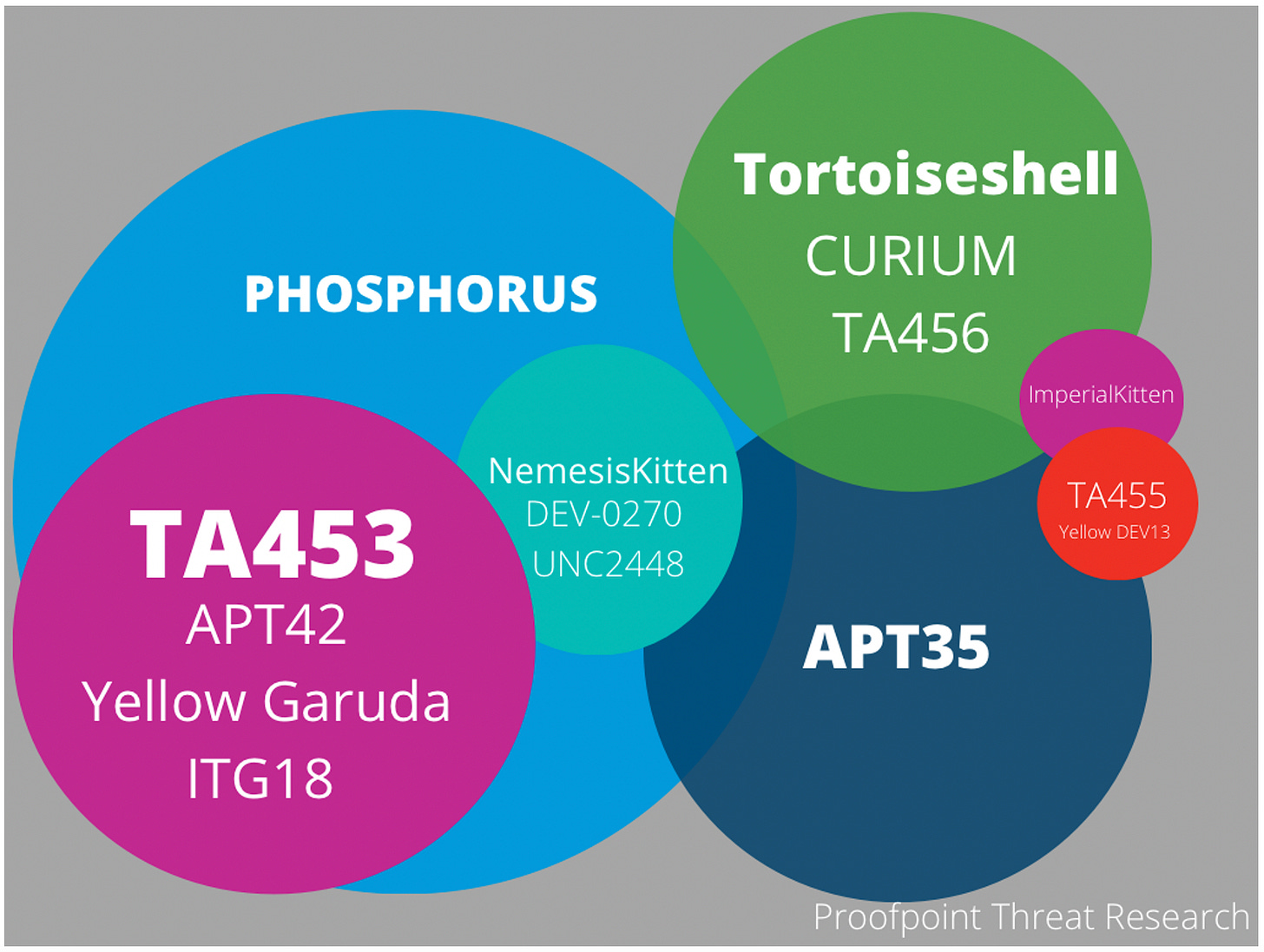
📧 It’s not unusual for nation-state hacking crews to adjust their approaches in response to ever changing and expanding priorities. This is also complemented by ever-evolving updates to their tools, tactics, techniques, and targeting. The threat actor tracked as Charming Kitten (aka APT42, PHOSPHORUS, TA453), an espionage group aligned with Iran’s Islamic Revolutionary Guard Corps (IRGC), used compromised email accounts, malware, and confrontational lures to go after a wide range of targets from at least late 2020 and through 2022, marking a deviation from the group’s traditional phishing techniques. It’s suspected that the kinetic campaigns reflect a flexible mandate to IRGC intelligence requirements. Some of the attack chains in late 2021 and early 2022 also involved the deployment of a backdoor called GhostEcho, a modular PowerShell-based framework that’s used to establish persistence, gather information, and execute commands. [Proofpoint]
📷 The Anker fiasco continues. The company, which found itself in a controversy after it emerged that its Eufy security cameras suffer from numerous privacy and security lapses, has now taken the step of removing as many as 10 commitments to safeguard user data. That said, the company has also made it clear that customers can access footage through a web portal and that users can “choose to store” the video clips in the cloud. It also attempted to explain some of the confusion, admitting that “Eufy Security’s Live View Feature on its Web-Portal Feature Has a Security Flaw.” It, however, hasn’t elaborated on why unencrypted streams can be accessed at all and if it shares video footage with law enforcement. [The Verge / Eufy]
🧱 Security analysts have discovered two API security vulnerabilities in BrickLink.com, LEGO Group’s official second-hand and vintage marketplace for LEGO bricks. The issues could have enabled attackers to take over user accounts, leak sensitive data stored on the platform, and even gain access to internal production data to compromise corporate servers. [Salt Security]
📞 Amid the ongoing war in Ukraine, phone calls from Russian soldiers to their family members are being intercepted by the Ukrainian military for potential intelligence and fodder for propaganda. [The Guardian]
ℹ️ U.S. government agencies are relying on data brokers for fraud detection and prevention, in part due to a loophole in the 1974 Privacy Act that limits the government’s use and sharing of records between federal entities. This has allowed “data brokers to hoover up millions of Americans’ data from public records and sell it back to the U.S. government.” [Politico]
🩺 The crippling ransomware attack on All India Institute of Medical Sciences (AIIMS), one of the leading hospitals in the nation, highlights the risk of digitizing health records without pushing for adequate security measures. [NPR / Security Week]
🔑 Access management giant Okta had some of its source code copied after an intruder gained unauthorized access to its private GitHub repositories. The revelation is just the latest in a series of security disclosures the company has made throughout the year. [The Hacker News]
👀 A little-known phone monitoring and stalkerware app called Xnspy has stolen data from tens of thousands of iPhones and Android devices without their users’ knowledge. The software is alleged to have been developed by a Lahore-based startup known as Konext. [TechCrunch]
📰 A large-scale advertising fraud campaign using Google Ads and “popunders” on high-traffic adult sites is estimated to have generated millions of ad impressions on stolen articles, making the fraudsters an estimated $275,000 per month. The threat actor is suspected to be of Russian origin. The clever technique involves serving the adult content as an iframe placed on top of a WordPress blog. When users click a video or a thumbnail, it triggers a real ad click on the popunder page underneath. What’s more, the blog content is also refreshed at regular intervals to serve new ads each time. [Malwarebytes]
⌛ It’s been a year since the brutal Log4j vulnerability (aka Log4Shell) came to light. The flaw in the ubiquitous open-source logging library exposed a wide range of applications and services, and while it no longer poses the software supply chain threat it once did, the bug continues to be still present in far too many systems worldwide, making it an endemic vulnerability that will continue to be exploited for years to come. According to Censys, from December 2021 to December 2022, there has been a 78% decrease in hosts vulnerable to Log4Shell — however, there are still over 23,000 hosts that appear to be vulnerable. [Censys]
🔓 Researchers have detailed a technique called Blindside that could render endpoint detection and response (EDR) platforms blind by unhooking the user-facing mode of the Windows kernel (NTDLL) from hardware breakpoints. Because EDR solutions rely heavily on hooks to track behaviors and malicious activities, the method could make behavior-based detection ineffective. [Cymulate]
🍪 France’s data privacy watchdog, CNIL, has issued Microsoft a €60 million fine for several violations related to how the Bing search engine handles cookies. It said that when users visited Bing.com, cookies were deposited on the machines without their consent and that two clicks were needed to refuse all cookies, as opposed to just one to accept all of them. [The Hacker News]
🗄️ The past few weeks in data breaches, leaks, and ransomware: Acuity Brands, ALMA Observatory, Amnesty International Canada, Bed Bath & Beyond, BTC.com, India’s Central Board of Higher Education, Chegg, CloudSEK, Continental, DraftKings, Empresas Públicas de Medellín, Experian, ForceNet, FuboTV, Gemini, The Guardian, H-Hotels, Hospital for Sick Children, Infosys, InfraGard, Maple Leaf Foods, Mercury IT, Metropolitan Opera, North Idaho College, PG&E, Rackspace, Radio Free Asia, Sargent & Lundy, Sequoia, Sobeys, Social Blade, Teqtivity, Thales, Thyssenkrupp, TPG Telecom, Twitter (1) (2), Vodafone Italy, VTB, and Whoosh.