Sophisticated operation targets XZ Utils
The XZ Utils backdoor incident has sent shockwaves through the open-source community
A roundup of some of the noteworthy developments in the cybersecurity landscape, encompassing the latest vulnerability discoveries and emerging attack trends. Here are this edition’s top stories -
↘️ Researchers from Augusta University have demonstrated a new acoustic side-channel attack on keyboards that can deduce user input based on their typing patterns, even in environments with noise, achieving an average success rate of 43%. The attack, however, hinges on compromising a target's system using other means (e.g., breach) to deploy a software capable of gathering typing samples in their working environment, including the text and the ambient noise. [arXiv]
↘️ The U.K. and the U.S. called out a Chinese state-affiliated threat group tracked as APT31 for perpetrating sweeping hacking operations against businesses, government officials, dissidents, and politicians. In some cases, this also included targeting the victims’ spouses. The U.S. also accused seven Chinese nationals and a front company named Wuhan Xiaoruizhi Science and Technology Company Limited of orchestrating an elaborate and invasive state-backed hacking program that goes back over a decade and targeted critical infrastructure. The Wuhan-based company serves as a cover for China’s state-sponsored apparatus, the governments said. The latest developments come following persistent warnings from Western governments about the hacking threat posed by Chinese hacking groups. FBI previously accused China of running “the biggest hacking program in the world by far.” [The Hacker News / CyberScoop / Reuters / The Guardian]
↘️ The Cyber Crime Center (DC3) of the U.S. Department of Defense (DoD) said it has reached the milestone of processing its 50,000th vulnerability report since its inception in November 2016. [DC3]
↘️ A first-of-its-kind study has devised attacks leading to wireless charger takeover via power supply voltage manipulation. The theoretical attacks, dubbed VoltSchemer, take aim at vulnerabilities in wireless charging systems that could allow adversaries to overheat charging devices, deliver inaudible voice commands to assistants like Siri and Google Assistant, and bypass Qi standard’s mechanisms to damage items exposed to intense magnetic fields. The attacks “grant attackers control over commercial-off-the shelf wireless chargers merely by modulating the voltage from the power supply,” the researchers said. “The core issue facilitating our attacks is the insufficient noise suppression in certain frequency bands, leaving systems vulnerable to interference. This gap makes all wireless charging technologies potentially vulnerable to interference-based attacks, particularly high-power systems like electric vehicle (EV) wireless charging.” [arXiv]
↘️ A novel attack called PrintListener could be used to infer fingerprint pattern features used during authentication by recording users’ finger-swiping friction sounds using either social media and online meeting apps like Skype, FaceTime, and WeChat or via malware with recording permissions. [NDSS]
↘️ The U.S. government has recommended a series of steps that critical infrastructure operators should take to prevent various kinds of distributed-denial-of-service (DDoS) attacks (volumetric, protocol-based, or Layer 7), including regularly analyzing network traffic to identify any traffic spikes, implementing CAPTCHA barriers, and keeping systems up-to-date. [CISA]
↘️ More than 125 million user records containing names, email addresses, phone numbers, billing information, and close to 20 million plaintext passwords have been exposed on the public internet by misconfigured Firebase instances, a new research has found by scanning more than five million domains. [env.fail]
↘️ Apple is facing a sweeping antitrust lawsuit in the U.S. that alleges that the company uses privacy and security as an “elastic shield” to serve its own interests, and that it has failed to extend end-to-end encryption protections for iPhone users that text Android users or iPhone users that don’t use iMessage. In both cases, the conversation flips to SMS, an insecure standard that’s not encrypted and prone to eavesdropping attacks. [The Hacker News / WIRED]
↘️ A group of researchers has found a serious security vulnerability in Apple’s M-series of chips — dubbed GoFetch — that would allow attackers to steal secret keys from Mac and iPad devices. [Ars Technica / Kim Zetter / The Hacker News / Dark Reading]
↘️ The leak of internal documents associated with a Chinese private firm called i-SOON (aka Shanghai Anxun Information Technology) has laid bare its inner workings and the various cyber espionage operations the company has supported on behalf of Beijing. This includes clusters tracked as RedAlpha, RedHotel, and POISON CARP. The revelations, offering a rare glimpse into the commercial spying ecosystem, also showcase China’s contracting of private firms to infiltrate an array of organizations worldwide, including in India, Kazakhstan, Korea, Malaysia, Mongolia, Taiwan, Thailand, the U.K., and Vietnam, as well as spy on domestic dissidents and ethnic minorities.
Among the tools advertised by the company are systems it claimed could hack into Microsoft Outlook and Gmail mailboxes and expose Chinese citizens using banned foreign platforms such as X and Telegram. The cache of leaked materials also describe the covert tools that were designed to look like a power strip or a battery bank, and which could breach local Wi-Fi networks.
The leaked chats and images show i-SOON's clients gave the company a list of targets they wanted to infiltrate. They also indicate the firm tried to recruit new talent by hosting a series of hacking competitions across China. Furthermore, i-SOON is said to have orchestrated money-driven ransomware campaigns on the side to offset budget cuts from the Chinese government. The discoveries underscore how China's private cybersecurity sector is pivotal in supporting China's aggressive APT attacks globally.
The exact source of the unprecedented leak is still unknown a month later, but i-SOON employees have confirmed the authenticity of the information. [The Hacker News / The Record / Dark Reading / CyberScoop / Risky Biz / TechCrunch / Krebs on Security / The Washington Post / The New York Times / Financial Times / WIRED]
↘️ Africa witnessed at least 189 documented disinformation campaigns, about four times the number reported the previous year, indicating a dramatic increase in influence operations against African nations and international agencies operating on the continent. [Dark Reading]
↘️ Newly unsealed court documents show that Meta launched a secret project called Ghostbusters to intercept and decrypt the network traffic from people using Snapchat, YouTube and Amazon to help it understand user behavior and better compete with its rivals. This was accomplished by leveraging custom apps from a service called Onavo, which Facebook acquired in 2013 and shut down in 2019 after it came under scrutiny for using its products to track users' web activity related to its competitors and secretly paying teens to capture their internet browsing patterns. Specifically, this materialized in the form of kits that could be installed on iOS and Android by distributing them via third-parties like GFK, SSI, YouGov, and uTest under the guise of low-key market research studies at least since 2016. These apps, it's alleged, installed a root Certificate Authority allowing Facebook to intercept and analyze panel participants’ internet usage. [Gizmodo / TechCrunch / Ars Technica / The Register]
↘️ Popular instant messaging app Telegram — which has over 900 million active users — has kicked up a privacy storm following the introduction of a controversial feature called Peer-to-Peer Login that grants users a free premium membership in exchange for allowing the platform to utilize their phone numbers as a relay for sending one-time SMS passwords to other users attempting to log into the platform. Telegram has warned that it “will not be liable for any inconvenience, harassment or harm resulting from unwanted, unauthorized or illegal actions undertaken by users who became aware of your phone number through P2PL.” [The Hacker News]
↘️ Attackers are targeting Apple iPhone users with MFA bombing attacks that use a relentless flood of legitimate password-reset notification alerts in an attempt to take over their iCloud accounts. The notification spam appears to leverage a target’s phone number or email address associated with an iCloud account to initiate a password reset via Apple’s iForgot page by somehow bypassing rate limiting restrictions. [Krebs on Security / The Hacker News / Dark Reading / Ars Technica]
↘️ The Android banking malware known as Vultur has been updated with new capabilities, allowing operators to remotely interact with the infected devices and modify files. First documented in early 2021, the latest version packs significantly more features and improved anti-analysis and detection evasion techniques, allowing the malware to bypass lock screen protections and harvest a wide range of data. [The Hacker News]
↘️ Google has announced a new security feature called Device Bound Session Credentials (DBSC) that binds browser authentication sessions to the device to combat cookie theft malware that allows threat actors to hijack user accounts. This relies on authentication with a private key created on device to keep users’ sessions secure. The only information sent to the server is the per-session public key which the server uses to certify proof of private key possession. [The Hacker News]
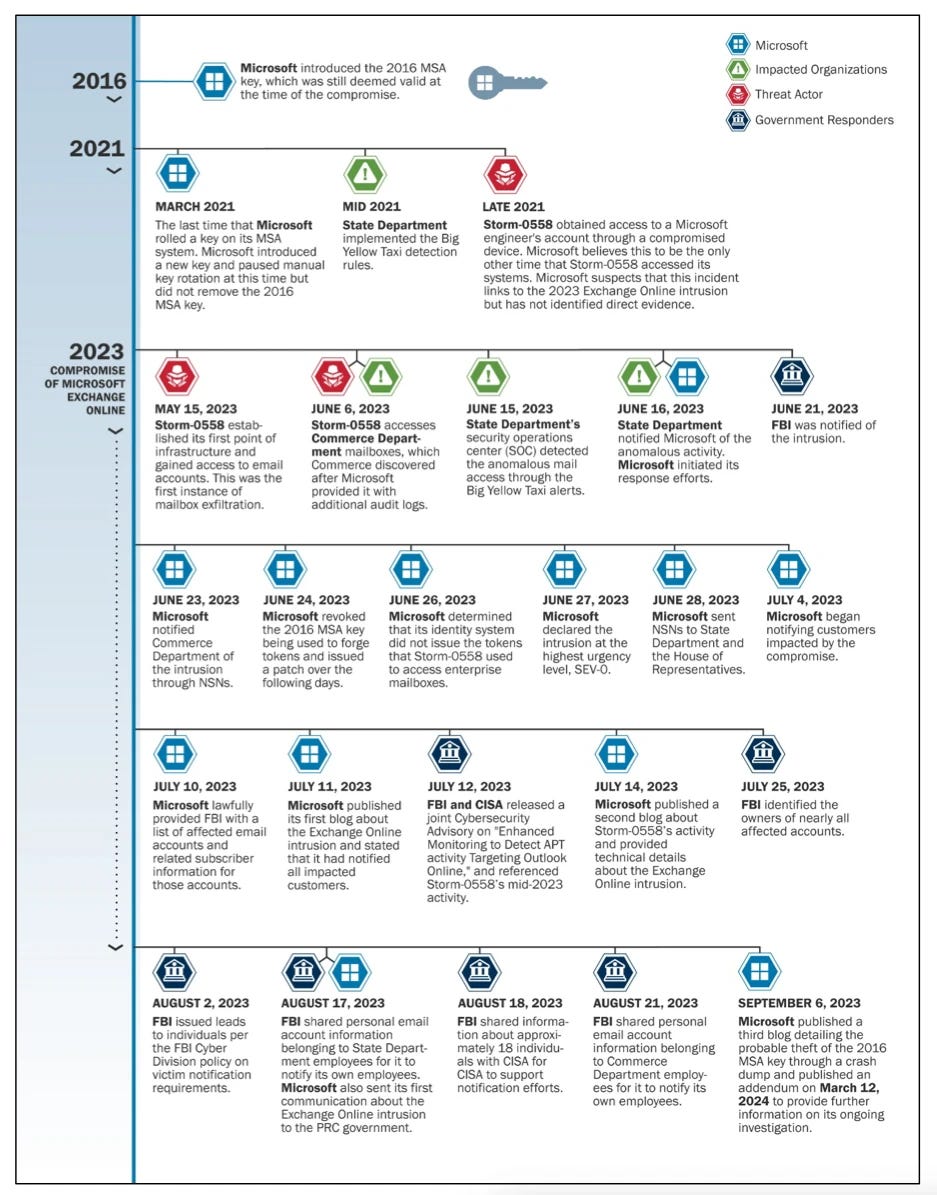
↘️ Microsoft has admitted that it’s still unsure of how and when Chinese nation-state actors tracked as Storm-0558 obtained a Microsoft Services Account (MSA) signing key that the company had issued in 2016 and used to sign forged authentication tokens to access the email accounts belonging to consumers and enterprises in May 2023. The key was originally set to be retired in March 2021, but was delayed, essentially allowing the adversary to use the consumer key-signed tokens to gain access to enterprise email accounts. While Microsoft initially claimed the key was obtained from a crash dump, it has since been found to be erroneous.
The U.S. Department of Homeland Security’s Cyber Safety Review Board (CSRB) criticized the company for its lack of transparency in public communications and for failing to limit the scope of key’s use (the same key could be used to forge tokens that worked for both consumer and enterprise accounts as opposed to just the former). “Microsoft’s security culture was inadequate and requires an overhaul, particularly in light of the company’s centrality in the technology ecosystem and the level of trust customers place in the company to protect their data and operations,” the CSRB said in its months-long review of the intrusions. “[The decisions] point to a corporate culture in Microsoft that deprioritized both enterprise security investments and rigorous risk management.” The board also recommended a comprehensive overhaul of Microsoft’s security infrastructure. [The Hacker News / Ars Technica]
↘️ Microsoft developer Andres Freund rocked the world when he revealed a backdoor had been intentionally planted in XZ Utils, an open-source data compression utility integrated within Linux and other Unix-like operating systems. The deliberate sabotage, although a near miss, could have “carved out a secret door” to millions of Linux systems across the world. In what’s a carefully crafted supply chain attack, the threat actors behind it spent over two years laying the social engineering groundwork, building their credibility in the open-source community under the name Jia Tan before rising to the status of a co-maintainer of the project and ultimately making malicious commits containing the backdoor to versions 5.6.0 and 5.6.1.
Tan’s elevation to being a co-maintainer was no fluke. It played out in an online mailing list where XZ Utils’ primary (and only) developer was criticized for not making updates to the software quickly enough. These accounts, which came out of nowhere and presumed to be sockpuppets, pressurized them into ceding control to another person. That responsibility fell on Tan given that they had been already contributing to the project. It has since emerged that the network of personas, including Tan, also made a subsequent push to get the backdoored version of XZ Utils to be included in Debian and Red Hat Linux versions.

The implant slipped into liblzma — a library part of XZ Utils and buried deep in the code in binary test files — essentially tampered with sshd to achieve remote code execution on the device and take control of it. OpenSSH, the most popular sshd implementation, doesn't link liblzma, but Debian and other Linux distributions add a patch to link sshd to systemd, which, in turn, links to liblzma, and this allows the malware to exert control over sshd. It's currently not known what code the attacker planned to run. While the inadvertent discovery narrowly avoided a large-scale security catastrophe, the incident betrays a sophisticated, meticulous operation aimed at poisoning the open-source ecosystem.
Exactly who is who is behind the campaign is a mystery, but it has all the hallmarks of a persistent cyber espionage operation. A timeline of Tan’s commits to GitHub alludes to them based in China (as does the name), although researchers have identified inconsistencies in the time zone in the commits metadata as well as times when commits were made during Chinese national holidays, suggesting it could be a misdirection. The XZ Utils hack also brings into stark relief the risks of backdooring volunteer-run projects and under-investing in the security of the open-source software supply chain that enterprises rely on.
With most open-source projects underfunded and run by a single or small group of maintainers, social engineering attacks on them isn't surprising and should set alarm bells ringing about how malicious actors are preying on exhausted developers to poison the ecosystem. What makes it even more troubling is the fact that the entire mechanism is opaque, with components and projects critical to modern digital infrastructure often maintained by unknown aliases and individuals scattered across the world. This makes open-source projects even more vulnerable to adversaries looking to find a way into enterprise networks. [The Hacker News / Ars Technica / WIRED / The Intercept / The New York Times / Reuters]
↘️ A new report from Google and Mandiant found that spyware and zero-day exploits increasingly go hand-in-hand, with a chunk of the 97 zero-days exploited in the wild in 2023 exploited by commercial surveillance vendors (CSVs). The findings come against the backdrop of a steady push by the U.S. government to curtail the abuse and proliferation of spyware to eavesdrop on journalists and activists. “CSVs operate with deep technical expertise to offer ‘pay-to-play’ tools that bundle an exploit chain designed to get past the defenses of a selected device, the spyware, and the necessary infrastructure, all to collect the desired data from an individual’s device,” the report said. [The Hacker News]
↘️ Cybercriminals are directly reaching out to T-Mobile and Verizon employees on their personal and work phones, trying to tempt them with as much as $300 to perform illegal SIM swaps, giving scammers full access to a victim’s cell phone number, and allowing them to receive multi-factor authentication text messages used to break into other accounts. [The Mobile Report / Reddit]
↘️ An illicit service called Spy.pet — launched in October 2023 — has been found to scrape Discord and sell billions of public messages posted by users on more than 10,000 servers for dirt cheap prices. The service’s creator is also offering the data for training AI models or to assist law enforcement agencies. [Stack Diary / The Register / 404 Media / Ars Technica]